Remove VanHelsing Ransomware
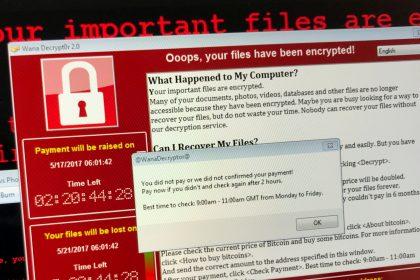
VanHelsing ransomware is a highly dangerous file-encrypting malware that employs double extortion…
Remove Jett Ransomware
Jett ransomware is a dangerous file-encrypting malware designed to lock users' data…
Lucky (MedusaLocker) Ransomware
Ransomware continues to be one of the most damaging forms of malware…
Venom Loader: Understanding the Malware Threat and How to Remove It
Venom Loader is a newly identified malware loader that has been linked…
PackUNWAN Malware: A Comprehensive Guide
Malware continues to pose significant risks to individuals and organizations alike. One…
VEZA Ransomware Threat: Prevention, Risks, and Recovery Strategies
VEZA Ransomware is yet another malware strain that is a part of…
QEPI Ransomware: A Menace from the STOP/Djvu Ransomware Lineage
QEPI Ransomware emerges as a sinister iteration within the notorious STOP/Djvu Ransomware…
WPTHRIVEHYPE: A Comprehensive Guide to Understanding and Removing This Cyber Threat
In the realm of cybersecurity, vigilance is paramount. One such threat that…
RinCrypt 3.0 Ransomware: A Menace in the Cyber Realm
RinCrypt 3.0 stands out, among its ilk, as a particularly insidious strain…
GooseEgg Malware: Threat Analysis and Removal Guide
GooseEgg, a stealthy predator, preying on unsuspecting users and their digital assets,…