RinCrypt 3.0 stands out, among its ilk, as a particularly insidious strain of ransomware, wreaking havoc on individuals and organizations alike. With its sophisticated encryption algorithms and extortion tactics, RinCrypt 3.0 poses a significant threat to data security and privacy.
Understanding RinCrypt 3.0 Ransomware
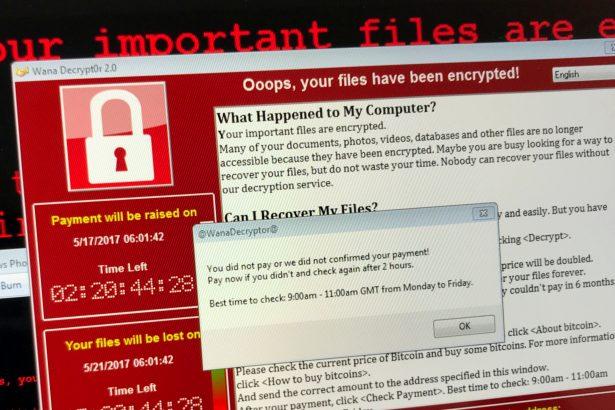
RinCrypt 3.0 operates on a familiar modus operandi common to ransomware: it infiltrates systems, encrypts valuable files, and demands a ransom for their release. The initial infection often occurs through malicious email attachments, compromised websites, or exploiting vulnerabilities in outdated software. Once inside a system, RinCrypt 3.0 swiftly encrypts files using strong encryption algorithms, rendering them inaccessible to the user.
Actions and Consequences
The consequences of a RinCrypt 3.0 infection can be catastrophic. Victims find themselves locked out of their own files, unable to access critical documents, photos, or other data essential for personal or business operations. The ransom note left behind by the attackers typically demands payment in cryptocurrency in exchange for a decryption key. However, there is no guarantee that paying the ransom will result in the recovery of files, and it may further incentivize cybercriminals to continue their malicious activities.
Detection Names and Similar Threats
RinCrypt 3.0 may be detected by various security software under different names, including but not limited to:
- Trojan-Ransom.Win32.RinCrypt
- Ransom:Win32/RinCrypt
- Win32/Filecoder.RinCrypt
Similar threats to RinCrypt 3.0 include notorious ransomware strains like WannaCry, Ryuk, and Maze, each with its own methods and characteristics but sharing the common goal of extorting victims for financial gain.
Removal Guide for RinCrypt 3.0 Ransomware
Removing RinCrypt 3.0 from an infected system requires a systematic approach to ensure complete eradication. Follow these steps carefully:
- Disconnect from the Internet: Immediately disconnect the infected device from the internet to prevent further communication with the attacker’s command and control servers.
- Enter Safe Mode: Restart the infected computer and enter Safe Mode. This will prevent RinCrypt 3.0 from loading during startup, making it easier to remove.
- Identify Malicious Processes: Use Task Manager to identify any suspicious processes running on the system. Look for unfamiliar or unusual processes that may be associated with RinCrypt 3.0.
- Terminate Malicious Processes: Once identified, terminate the malicious processes to halt the ransomware’s activities temporarily.
- Delete Malicious Files: Navigate to the directories where RinCrypt 3.0 may be residing and delete any associated files. Be cautious not to delete system files essential for the operating system’s functionality.
- Restore from Backup: If possible, restore encrypted files from a backup created before the infection occurred. This is the most reliable method of recovering data without paying the ransom.
- Scan with Antivirus Software: Perform a thorough scan of the system using reputable antivirus or antimalware software to detect and remove any remaining traces of RinCrypt 3.0.
- Update Security Software and Operating System: Ensure that your antivirus software and operating system are up to date with the latest security patches to protect against future threats.
Preventing Future Infections
Prevention is key to safeguarding against ransomware attacks like RinCrypt 3.0. Here are some best practices to minimize the risk of infection:
- Educate Users: Train users to recognize phishing attempts and avoid clicking on suspicious links or downloading attachments from unknown sources.
- Keep Software Updated: Regularly update all software, including operating systems, web browsers, and plugins, to patch known vulnerabilities that ransomware may exploit.
- Use Antivirus Software: Install reputable antivirus software and keep it updated to detect and remove ransomware and other malware threats.
- Backup Data Regularly: Implement a robust backup strategy to regularly back up important files and ensure they are stored securely offsite or on a separate network.
- Enable Firewall: Enable firewalls on all devices to monitor and control incoming and outgoing network traffic, preventing unauthorized access to your system.
By staying vigilant and implementing these preventive measures, individuals and organizations can fortify their defenses against the pernicious threat of RinCrypt 3.0 and similar ransomware strains.