Cyber Threats
Discover Categories

Malware

Adware

Browser Hijackers

Ransomware

iPhone Threats

Android Threats

Mac Malware

Cybersecurity for Business
Latest News
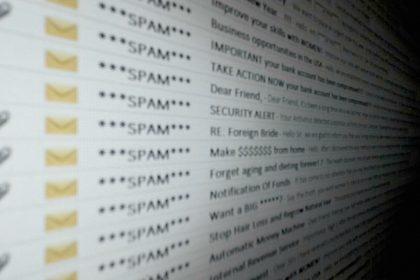
“Wire Transfer To Your Diocesan Account” Scam
The "Wire Transfer To Your Diocesan Account" email is a malicious spam campaign designed to trick recipients into opening a…
Qv Ransomware
Qv ransomware is a file-encrypting threat that locks personal and business data, renames affected files with a unique victim ID…
Ad Blocker Unlimited Adware
Ad Blocker Unlimited claims to block advertisements and trackers, but analysis shows it behaves like adware instead. Rather than improving…
FIFA 2026 World Cup Scams
Fake FIFA ticket sites, merchandise stores, hospitality offers, and phishing pages are targeting football fans ahead of the 2026 World…
“FedEx e-Order Notification” Email Scam
Fraudulent FedEx shipping notification designed to deliver malware through a malicious Excel attachment. Threat Summary CategoryDetailsThreat TypePhishing Email, Malspam Campaign,…
Why Cybersecurity Is Important for Small and Medium Businesses (SMBs)
Cybersecurity is no longer a concern reserved for large corporations. Small and medium businesses (SMBs) are increasingly becoming targets of…
MetaMask Crypto Malware
What Is MetaMask Crypto Malware? MetaMask Crypto Malware is a broad term used to describe malicious software, phishing campaigns, rogue…
Scan Your System for Malware
Don’t leave your system unprotected. Download SpyHunter today for free, and scan your device for malware, scams, or any other potential threats. Stay Protected!
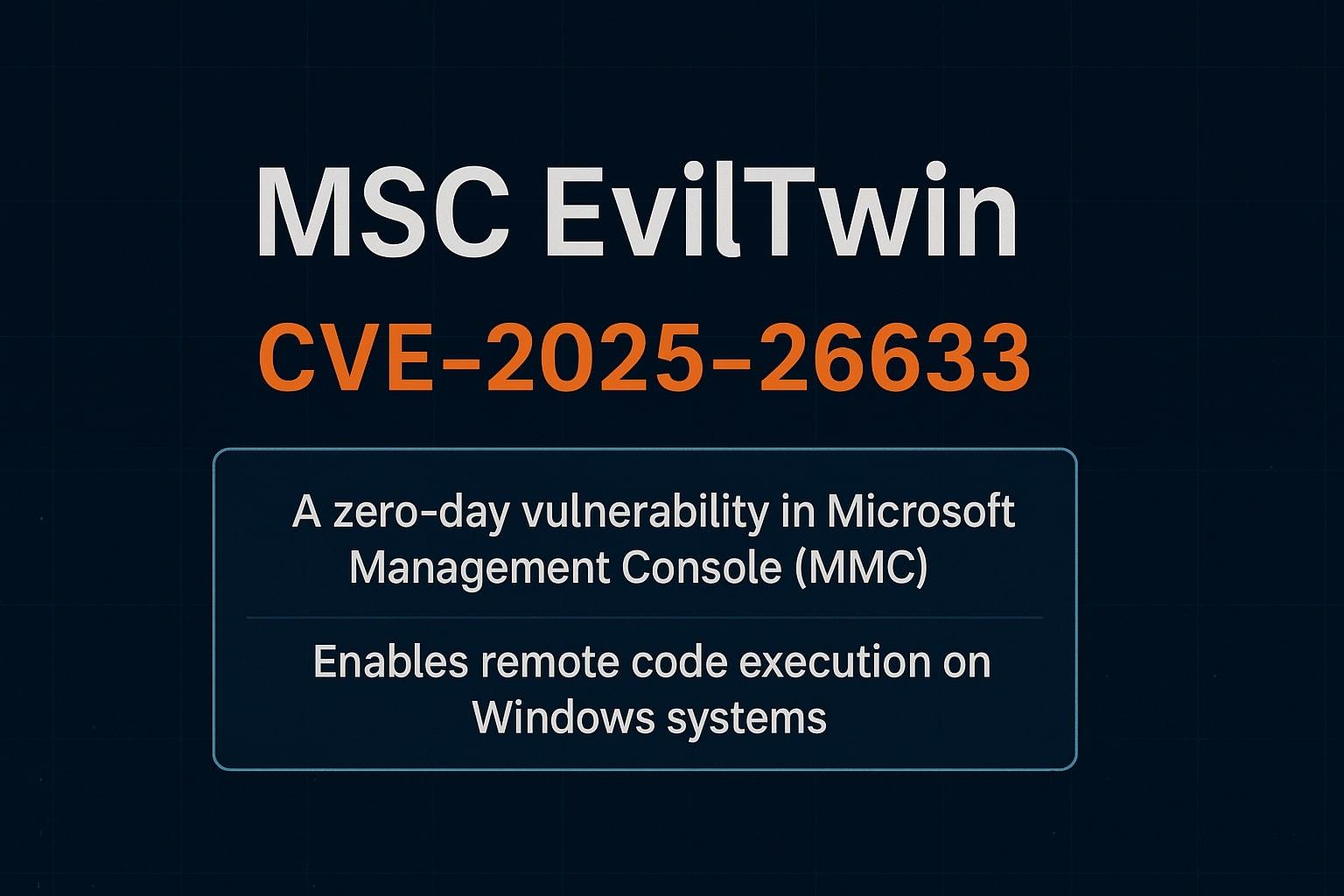
CVE Vulnerabilities
ITFunk - Watch it