“Confirm That This Is Your Valid Email Address” Phishing Scam
Phishing scams are a pervasive threat in today’s digital landscape, designed to deceive individuals into revealing sensitive information or installing…
“Website Suspension in Progress” Phishing Scam: Fighting Email Scams
Phishing scams are deceptive tactics used by cybercriminals to trick individuals into divulging sensitive information, such as usernames, passwords, or…
“I’ve Got Access to Your Smartphone” Email Scam: A Comprehensive Guide to Protecting Yourself
Phishing scams are a constant threat in today’s digital world, evolving with each new tactic to deceive unsuspecting victims. One…
Missed Call Voicemail Alert Scam: A Phishing Threat to Watch Out For
Phishing scams have become increasingly sophisticated, using clever tactics to deceive users into divulging sensitive information or installing harmful software.…
Rothschild Foundation Email Scam: A Dangerous Phishing Threat and How to Protect Yourself
Phishing scams have become an increasingly common threat, targeting individuals and businesses alike. These deceptive schemes typically present themselves as…
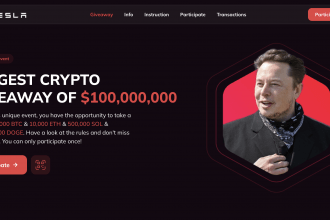
Elon Musk X Donald Trump Crypto Giveaway Scam
Cybercriminals are constantly evolving their tactics, creating scams that prey on users' trust in high-profile figures. One such scheme is…
Effetmanapp: What is Adware and How to Protect Yourself Against it?
Adware is a form of malware designed to deliver intrusive advertisements to users. These ads often promote questionable websites, unwanted…
“Your Device Is at Risk” Pop-up Scam on Mac: How to Remove It and Protect Your System
The "Your Device Is at Risk" pop-up scam is one of the many deceptive alerts targeting Mac users, designed to…
Email Resource Alert Triggered Email Scam: Understanding the Threat and How to Protect Yourself
Phishing scams continue to plague the digital world, exploiting unsuspecting individuals and their systems. One such malicious tactic is the…
Hack.TL Ver U99 B Buzz: A Form of Adware that Affects Users’ Systems
Adware is a form of malware designed to deliver unwanted advertisements on your computer, often leading to disruptive user experiences.…
Trojan.PowerShell.CoinStealer.RPMTB: Malware: Understanding the Threat
Trojans, or Trojan Horse malware, represent one of the most dangerous forms of malicious software. Named after the mythological Greek…
AvosLocker Virus: A Comprehensive Guide
Ransomware remains one of the most alarming types of malware, and the AvosLocker virus is a particularly notable variant. Known…
HLAS Virus Files: A Comprehensive Guide
Malware threats are becoming increasingly sophisticated, targeting unsuspecting users and wreaking havoc on their systems. One such threat is the…
“Removing Useless Files Is Advised” Pop-Up Scam
Pop-up scams are deceptive messages or alerts that appear unexpectedly on a user's screen, often during web browsing. These scams…
TL-Ver-T39-I-Buzz: Removal, Detection, and Prevention
New and sophisticated malware constantly emerges, posing significant risks to personal and professional data. One such threat currently making waves…
W64Devkit.exe Virus: A Removal Comprehensive Guide
The W64Devkit.exe virus is a sophisticated cyber threat that has been causing significant concern among users worldwide. This malware, often…
SpyAgent Malware: A Comprehensive Guide to Understanding, Removing, and Preventing Future Infections
SpyAgent malware emerges as a particularly insidious threat targeting Android devices. Designed to covertly monitor and collect sensitive information, SpyAgent…
Colony Ransomware: The Malace of .colony File Extension
Ransomware is a type of malicious software designed to deny access to a computer system or its data until a…
Ailurophile Stealer: Battling Trojan Malware
Trojan horse malware, commonly known as trojans, are a type of malicious software that disguise themselves as legitimate programs to…
“Email Suspension at Server Database”: Beware of the cPanel – Server Glitch Phishing Scam
Phishing is a form of cyber-attack where malicious actors impersonate legitimate entities to deceive individuals into revealing sensitive information or…
“Payment Approved by International Authorities” Phishing Scam: Avoiding Phishing Attacks
Phishing scams are deceptive attempts to acquire sensitive information by masquerading as a trustworthy entity. These scams typically come in…
Trojan.Win32.Inject4.JXoomn: A Stealthy Trojan Threat
Trojan horse malware, commonly referred to as "Trojans," are a type of malicious software designed to disguise themselves as legitimate…
Emansrepo Stealer: A Comprehensive Guide to Detecting, Removing, and Preventing Data Theft
Cybersecurity threats continue to evolve, with data-stealing malware becoming a growing concern for users and organizations alike. One of the…
Voldemort Backdoor Malware: How to Detect, Remove, and Prevent This Dangerous Cyber Threat
Cyber threats are becoming increasingly sophisticated and pervasive. One such threat is the Voldemort backdoor malware, a highly dangerous form…
Mykneads24.com Threat: Adware, Malware, and Malicious websites. What do You Need to Know?
Adware is a type of malicious software designed to display or download advertisements onto a victim's device without consent. These…
QuickSearch Browser Hijacker: A Detailed Cybersecurity Guide
Browser hijackers are a type of malware designed to manipulate web browsers without the user’s permission, often modifying settings to…
JSTimer Unwanted Browser Extension
JSTimer is classified as an unwanted browser extension, often categorized under the broader umbrella of potentially unwanted programs (PUPs) or…
Xin Ransomware: A Detailed Guide to Removing and Preventing Ransomware Invasion
Ransomware is a form of malicious software (malware) designed to encrypt files on a victim’s device, rendering them inaccessible until…
RAIRApp: Understanding Potentially Unwanted Programs (PUPs) and the Threat They Pose to Your Security
Potentially Unwanted Programs (PUPs) are software applications that, while not overtly malicious, are often deceptive and unwanted by users. These…
IOR Ransomware: A Comprehensive Guide to Ransomware Detection, Removal & Prevention
Ransomware is a form of malicious software designed to block access to a computer system or files until a ransom…
Beware of the ‘New Order from Start Group S.R.L’ Deception: How the Start Group S.R.L Email Scam Targets You
Phishing scams are one of the most common forms of online fraud today. Typically executed through email, phishing scams deceive…
TrialRocovery Ransomware: A Growing Cybersecurity Threat
Ransomware is a particularly destructive form of malware that encrypts the files on an infected system, rendering them inaccessible until…
TopVocEdClub: An Adware Threat
Adware is a type of malicious software designed to deliver unwanted advertisements to a user's computer. Unlike other forms of…
LadsStudio.com Adware: A Guide to Removing Annoying Ads
Adware, short for advertising-supported software, is a form of malware designed to display unwanted advertisements on your computer. Unlike traditional…
Luxy Ransomware: A Comprehensive Guide
Ransomware is a form of malware that encrypts files on a victim's system, rendering them inaccessible until a ransom is…
Cunt Ransomware: Removing Ransomware
Ransomware is a type of malicious software that restricts access to a computer system or its data, often by encrypting…
“More Convenient Way” Email Scam
Phishing scams have evolved significantly over the years, becoming increasingly sophisticated and difficult to identify. These scams often masquerade as…
SearchPlus Browser Hijacker: A Comprehensive Guide
Browser hijackers are a type of malicious software designed to compromise and manipulate web browsers. Their primary objective is to…
Claim Base Dawgz Scam Pop-Up
Pop-up scams are deceptive online threats designed to trick users into divulging personal information or downloading malicious software. These scams…
Tucarmex.xyz Adware: A Form of Malware
Adware is a category of malicious software that bombards users with unwanted advertisements, typically in the form of pop-ups or…
Avast Scan Phishing Scams
Phishing scams are a prevalent and dangerous form of cyberattack where malicious actors deceive individuals into providing sensitive information, such…
Ad Blocker Elite Extension Virus
In the vast landscape of digital threats, malware comes in various forms, each with its own method of infiltration and…
Trojan.Win32.Leonem Trojan Horse Malware: A Comprehensive Guide
Trojan horse malware, often referred to simply as a "Trojan," is a type of malicious software that disguises itself as…
Trojan:Win32/HeavensGate.RPYMTB Trojan Horse Malware
Trojan horse malware, commonly referred to simply as Trojans, is a type of malicious software designed to mislead users of…
Moneyistime Ransomware: A Growing Cybersecurity Threat
Ransomware is a type of malicious software (malware) designed to block access to a computer system or its data, typically…
Tickler Malware: Detection, Removal, and Prevention
Cyber threats are becoming increasingly sophisticated. One such threat that has recently gained notoriety is Tickler malware. This type of…
FindFast and the Threat of Browser Hijackers
Browser hijackers are a form of malware designed to infiltrate web browsers, alter their settings without user consent, and redirect…
GoogleDefender.info Adware: A Guide to Removing Annoying Ads
Adware, short for advertising-supported software, is a type of malicious software designed to deliver unwanted advertisements to users. Unlike traditional…
EagleSpy Malware on Android
In today’s interconnected world, mobile devices have become a prime target for cybercriminals, and one particularly insidious threat is the…
“Join Our Great Illuminati” Email Phishing Scam
Phishing scams are a significant threat in today’s digital age, where malicious actors exploit deceptive tactics to trick individuals into…