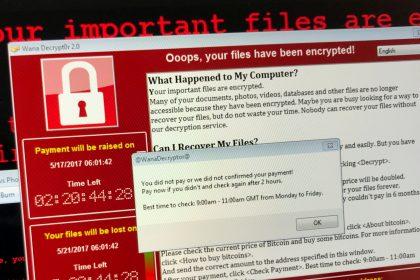
Dzen Ransomware: A Comprehensive Removal Guide
In the ever-evolving landscape of cyber threats, ransomware remains one of the…
.Water Ransomware: Actions, Consequences, and Removal Guide
The .Water ransomware has emerged as a ruthless member of the Phobos…
BackMydata Ransomware: A Comprehensive Guide
In the ever-evolving landscape of cyber threats, the BackMydata Ransomware has emerged…
Dx31 Ransomware: Unraveling the Threat and Protecting Your Data
In a recent inspection of malware samples submitted to VirusTotal, a new…
SomeOrdinaryGamers Mutahar: Unrelenting Ransomware Threat
In the perilous realm of cyber threats, SomeOrdinaryGamers Mutahar emerges as a…
Jopanaxye Ransomware: Actions, Consequences, and Prevention
In the labyrinth of cyber threats, Jopanaxye emerges as a ransomware variant…
Ransomware Alert: Unveiling the Menace of HuiVJope and Its Impact
In the realm of cybersecurity, the looming threat of ransomware casts a…
Phobos Ransomware Family Grows with Lizard Ransomware
Another strain of malware based on the notorious Phobos code has been…