Another strain of malware based on the notorious Phobos code has been discovered. It is named Lizard Ransomware and it has been discovered encrypting valuable files on numerous computers.
When Lizard Ransomware encrypts files, it changes the file’s original name by adding an ID string, an email address, and a new file extension to it. The generated ID string is unique to each victim, and the contact email address used by the hackers is ‘r3wuq@tuta.io.’ The file extension used is ‘.LIZARD,’ and that’s where the name of the threat originates from.
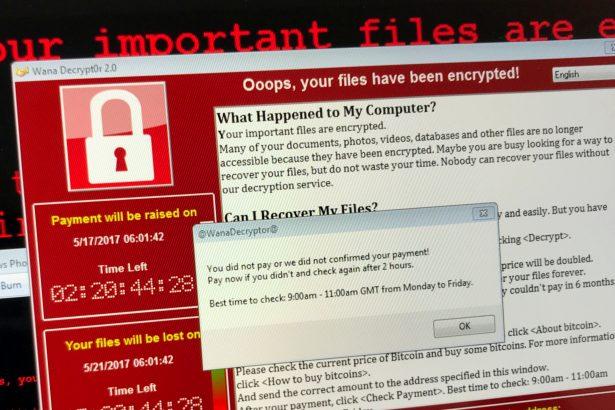
The ransom note associated with Lizard Ransomware comes in two forms. One is displayed in a pop-up window created from the ‘info.hta’ file, while the other is contained inside a text file named ‘info.txt.’
The ransom note in the text file instructs the victims to establish contact via ‘r3wuq@tuta.io.’ If victims do not hear from the hackers within 24 hours, they are instructed to use a Telegram account to establish contact, and that account is ‘@Online7_365.’
The hackers will only accept Bitcoin payments, and the ransom note also states that the hackers are willing to decrypt up to 5 files for free to prove they can unlock all the files upon receiving the ransom payment.
How Do I Deal with a Lizard Ransomware Attack?
To protect yourself from a Lizard Ransomware attack, you should have a reputable malware remediation tool installed on your computer. That way, you can constantly scan for objects associated with this troublesome ransomware infection, as well as other malware. Also, to mitigate the potential damage to your files, do not forget to back them up on an external hard drive or virtual cloud storage.