Care.Sale Adware
Care.Sale is a browser extension categorized as adware that claims to help users save money while shopping online. In reality, it floods browsers with intrusive advertisements, redirects users to questionable websites, and may monitor browsing activity. While it may look harmless at first, its behavior can expose users to scams, malicious downloads, and privacy risks. Once installed, the extension injects pop‑ups, banners, coupons, and other advertisements into web pages, disrupting normal browsing and potentially leading to unsafe sites. Care.Sale Adware – Threat Summary CategoryDetailsThreat TypeAdware, advertising‑supported browser extensionDetection NamesVaries by security vendors (often flagged as adware/PUP)SymptomsExcessive pop‑up ads, redirects to suspicious websites, slower browser performanceDamage & DistributionDisplays intrusive ads, collects browsing data, redirects to unsafe pages; distributed via bundled installers, deceptive pop‑ups, torrentsDanger LevelMediumSpyHunter Link →https://www.enigmasoftware.com/products/spyhunter/?ref=ywuxmtf How Care.Sale Adware Affects Your Browser Once installed, Care.Sale adware integrates directly into your browser as an extension. Its main purpose is to generate revenue by displaying advertisements. Typical behaviors include: Some ads promoted by Care.Sale may lead to scam pages, phishing sites, or downloads of additional unwanted programs. The extension may also request permissions to read and change data on websites, which gives it the ability to monitor browsing activity or alter page content. Where Care.Sale Adware Comes From Adware like Care.Sale rarely spreads through legitimate download channels. Instead, it usually sneaks into systems through deceptive distribution methods such as: 1. Software BundlingFree software installers often include additional components hidden in “Custom” or “Advanced” setup options. If users rush the installation process, the adware gets installed alongside the intended program. 2. Fake Pop‑Up AdsSome websites display misleading messages encouraging users to install browser extensions or update software. 3. Torrent and Freeware SitesUnverified download portals frequently bundle adware with free apps or media files.…
Esslymph.com
Esslymph.com is a website that has recently gained attention due to suspicious behavior reported by users and cybersecurity experts. While it does not appear to host malware directly, it exhibits traits commonly associated with adware, push notification spam, and browser hijackers. Visiting or interacting with this site may expose users to intrusive advertising, misleading prompts, or unsafe downloads. Understanding how esslymph.com operates and how to protect your system is crucial for safe browsing. What Esslymph.com Does The site’s behavior is primarily related to browser manipulation and unwanted advertising. Users may experience: Although esslymph.com is not classified as a virus, these behaviors make it potentially harmful, especially for users who may unknowingly engage with its content. How Users Encounter Esslymph.com There are several common ways users end up on esslymph.com: Once users are redirected, the site may attempt to manipulate browser settings or encourage downloads that could compromise system security. Security Risks Associated With Esslymph.com Even though esslymph.com does not install malware by itself, interacting with the site carries several risks: These risks highlight the need to treat esslymph.com as a suspicious site rather than a safe or trustworthy source. How to Protect Yourself From Esslymph.com If your browser is being redirected or you notice frequent pop-ups from esslymph.com, take the following steps: These measures can reduce the risk of ongoing exposure to unsafe content and protect your personal data. Conclusion Esslymph.com is not a legitimate or trustworthy website. While it does not appear to be direct malware, its behavior is consistent with adware, browser hijackers, and aggressive advertising schemes. Users should avoid interacting with the site, remove any associated adware or suspicious extensions, and maintain vigilant browsing habits. Treat any appearance of esslymph.com on your device as a warning sign of potential unwanted software already present in your system.
Digitalonlinesafety.com
Digitalonlinesafety.com may appear at first glance to be a legitimate online safety platform, but the website has multiple characteristics that raise serious security concerns. Many users encounter it unexpectedly through redirects or pop-ups, and its design and behavior suggest it could be part of scareware tactics that try to manipulate users into downloading unnecessary or potentially harmful programs. Understanding the risks and learning how to protect your devices is critical. Table of Threat Information FeatureDetailsThreat TypeSuspicious Security/Scareware WebsiteDetection NamesNot officially detected by major antivirus as malware, but flagged as risky or untrustworthySymptomsUnexpected redirects, pop-up security alerts, download prompts, frequent browser warningsDamage & DistributionMay lead to unwanted programs, adware, or phishing sites; spread via browser redirects, pop-ups, or bundled softwareDanger LevelModerate to High – primarily social engineering risk and potential for adware installationSpyHunter LinkSpyHunter Anti-Malware Understanding Digitalonlinesafety.com Digitalonlinesafety.com is not an established cybersecurity platform. Instead, it demonstrates several red flags common to sites designed to manipulate visitors through fear: These factors indicate that Digitalonlinesafety.com is more focused on tricking users than providing genuine cybersecurity information. How Users Encounter Digitalonlinesafety.com Most people do not visit this site intentionally. It often appears through indirect methods: Repeated exposure often indicates an underlying adware or PUP infection rather than a problem caused by the website itself. How Digitalonlinesafety.com Tries to Manipulate Users Digitalonlinesafety.com uses several strategies to make visitors act quickly without thinking: These tactics are classic scareware techniques: they exploit fear and urgency to convince users to take risky actions. Signs Your Device May Be Affected If you encounter Digitalonlinesafety.com frequently, your system may have adware, a browser hijacker, or other unwanted programs. Look for these symptoms: These signs indicate a compromised browsing environment rather than an isolated website issue. Protecting Your Device from Digitalonlinesafety.com Taking proactive steps can help secure your system and prevent further exposure: 1. Remove Unknown Programs and Extensions…
Zollo Ransomware
Zollo ransomware is a dangerous file‑encrypting threat that locks personal data and demands payment for a decryption key. Once it infiltrates a system, it encrypts files and leaves a ransom message instructing victims to contact attackers and pay for recovery. Victims quickly discover their documents, photos, and databases are no longer accessible. The attackers rely on social engineering and malicious downloads to trick users into executing the payload. After encryption is complete, victims are pressured into paying a ransom—often with no guarantee their files will actually be restored. Zollo Ransomware – Threat Summary CategoryDetailsThreat TypeRansomware / Crypto VirusEncrypted File ExtensionTypically adds a unique ransomware extension to encrypted filesRansom Note FilenameUsually dropped as a text or pop‑up message with instructionsEmail ContactProvided in the ransom note by attackersDetection NamesDetected by multiple antivirus engines as ransomware variantsSymptomsFiles cannot be opened; filenames changed; ransom message appearsDamageComplete file encryption; potential installation of additional malwareDistribution MethodsMalicious email attachments, pirated software, fake updates, unsafe downloadsDanger Level🔴 HighRemoval Tool →SpyHunter How Did I Get Infected With Zollo Ransomware? Zollo ransomware typically spreads through deceptive delivery methods designed to trick users into launching malicious files. The infection usually occurs when a user unknowingly runs a disguised payload. Common infection vectors include: Malicious Email Attachments Cybercriminals distribute spam emails containing infected attachments or links. These attachments may appear as invoices, delivery notifications, or important documents. Once opened, the ransomware payload executes and begins encrypting files. Fake Software Updates Attackers often distribute fake updates for popular programs such as browsers or media players. Instead of installing legitimate patches, the installer drops the ransomware. Pirated Software and Cracks Illegal activation tools and pirated downloads are a common source of ransomware infections. These files often include hidden malware that activates once the program runs. Untrusted Download Sources Freeware sites, torrent networks, and third‑party download portals are frequently used to distribute infected installers and bundled malware. What Zollo Ransomware Does to Your Files After Zollo ransomware gains access to the system, it begins scanning the computer for valuable files. Documents, images, databases, archives, and other important data are targeted first.…
Go Omnibar AI Redirect
Go Omnibar AI redirect is a browser hijacker that modifies browser settings and forces users to perform searches through the go.omnibar.ai domain. Once active, it changes the default search engine, homepage, or new tab page and intercepts search queries entered in the browser’s address bar. Although it may appear as a productivity or AI‑powered browsing extension, the underlying behavior is typical of potentially unwanted browser hijackers that track browsing activity and redirect traffic through affiliate links. Go Omnibar AI Redirect Threat Summary CategoryDetailsThreat TypeBrowser Hijacker, Redirect, Search HijackerAssociated Domaingo.omnibar.aiDetection NamesBrowserHijacker.Omnibar, PUA.OmnibarAI, Redirect.OmnibarSymptomsHomepage and default search engine changed, search redirects, unknown extensions installedDamage & DistributionBrowser tracking, forced redirects, promoted sponsored results; distributed via browser extensions or bundled installersDanger LevelMediumRemoval Tool →SpyHunter What Go Omnibar AI Redirect Changes in Your Browser Once the Go Omnibar AI redirect hijacker enters a browser, it begins modifying several settings to ensure users are forced through its search service. Typical changes include: Over time, this can result in: How Go Omnibar AI Redirect Hijacked Your Homepage Most users don’t intentionally install the Go Omnibar AI redirect browser hijacker. Instead, it arrives through deceptive methods such as: Bundled browser extensions Extensions promising AI search tools or productivity features may secretly change browser settings after installation. Free software installers Some freeware packages include additional browser extensions that users unknowingly accept during installation. Fake update prompts Malicious websites sometimes push “required extensions” to access certain features. Unverified Chrome extensions…
Cynanira.com Ads
Cynanira.com ads are intrusive browser notifications and redirect ads that appear after a user accidentally allows notifications from the site or installs adware. These ads may open suspicious pages, promote fake downloads, or redirect to potentially dangerous websites. While Cynanira.com itself is typically not a virus, the ads it pushes can expose your system to scams, malicious downloads, and privacy risks if ignored. Cynanira.com Adware Summary CategoryDetailsThreat TypeAdware / Browser Notification SpamDetection NamesAdware.Cynanira, PUA:Win32/Adware, Adware.GenericSymptomsConstant pop-ups, redirects, unexpected ads in the browser or desktop notificationsDamage & DistributionRedirects to malicious sites, installs unwanted extensions, tracks browsing dataDanger LevelMediumSpyHunter Removal Toolhttps://www.enigmasoftware.com/products/spyhunter/?ref=ywuxmtf How Cynanira.com Affects Your Browser Once Cynanira.com gains notification permission, it begins pushing advertisements directly to your desktop or browser. Typical behavior includes: Adware like this is designed to generate revenue through ad clicks or installs. Developers earn money whenever victims interact with these ads or install promoted programs. Over time, the ads may become more aggressive and disruptive, interfering with normal browsing. Where Cynanira.com Comes From Most victims encounter Cynanira.com through deceptive websites or bundled software downloads. Common infection sources include: Adware developers often hide installation options inside software installers so users unknowingly approve them. Once permission is granted, the browser allows the site to send notifications—even when the browser is closed. Is Cynanira.com a Real Threat? Cynanira.com ads might seem harmless, but they can lead to several problems: 1. Privacy Risks Adware may track browsing activity and collect information to serve targeted ads. …
Search-Serpey.com Hijacker
Search-Serpey.com is a deceptive search engine promoted through a browser hijacker that forces unwanted redirects and manipulates browser settings. Once installed, it can change your homepage, default search engine, and new tab settings to push traffic through its own domain. While it may look like a legitimate search tool, its main goal is advertising revenue and data collection rather than providing useful results. Browser hijackers like this often sneak onto systems through bundled software or misleading browser extensions. If left installed, they can expose users to intrusive ads, suspicious redirects, and potential privacy risks. Threat Summary – Search-Serpey.com Browser Hijacker FieldDetailsThreat TypeBrowser Hijacker / RedirectAssociated Domainsearch-serpey.comDetection NamesGeneric PUP detections, BrowserHijacker variantsSymptomsHomepage changes, search engine replaced, constant redirects, unwanted adsDamage & DistributionBrowser tracking, intrusive ads, redirects to questionable sites; spread via bundled installers and misleading extensionsDanger LevelMediumRemoval Tool →SpyHunter What Search-Serpey.com Browser Hijacker Changes in Your Browser The Search-Serpey.com browser hijacker takes control of key browser settings to force users to interact with its search engine. Once active, it typically: Fake search engines promoted by hijackers usually don’t generate their own results. Instead, they redirect queries to legitimate engines like Yahoo or Google while inserting sponsored content or tracking users. This redirection system allows the operators to earn affiliate revenue every time a user performs a search or clicks on ads. Another concern is data collection. Browser hijackers often monitor: This information may be shared with advertising networks or third parties, creating potential privacy risks. How Search-Serpey.com Hijacked Your Homepage Most victims don’t intentionally install the Search-Serpey.com hijacker. Instead, it usually arrives through one of these methods: Software Bundling Free software installers sometimes include extra programs hidden in the setup process. If users select “Quick” or “Recommended” installation, bundled add-ons may install automatically.…
“Giant Coupons Official Extension” Adware
Giant Coupons Official Extension pretends to help users find discounts and shopping deals, but it actually functions as adware that floods your browser with intrusive advertisements and tracks browsing behavior. Instead of improving your online shopping experience, it injects coupons, banners, and redirect links into websites you visit. Once installed, this extension can slow down your browser, generate aggressive pop-ups, and potentially expose you to scams or malware through malicious advertising networks. Threat TypeAdware / Advertising-Supported Browser ExtensionDetection NamesAdware.GiantCoupons, PUA:Win32/GiantCoupons, Adware.Plugin.GiantCouponsSymptomsPop-up ads, coupon banners, redirected shopping pages, slower browser performanceDamage & DistributionTracks browsing data, injects ads into websites, often bundled with free software or deceptive download pagesDanger LevelMediumRemoval ToolSpyHunter Adware like this is designed primarily to generate advertising revenue by injecting ads into web pages and redirecting traffic through affiliate networks. In many cases, it also collects browsing data such as visited sites, search queries, cookies, and device information. How Giant Coupons Official Extension Affects Your Browser After installation, Giant Coupons Official Extension integrates directly into your browser as an add-on. Its main purpose is to insert advertising content into pages you visit. Typical changes include: Many users notice that legitimate pages suddenly display extra promotional boxes, deal alerts, or auto-opening tabs. The extension can also modify website code to insert its own ads, meaning you’ll see advertising that isn’t actually part of the original website. Where Giant Coupons Official Extension Comes From Most users never intentionally install this extension. The adware commonly spreads through software bundling, where free programs secretly include additional extensions during installation. Common infection sources include: During installation, the extension may be hidden inside “Quick” or “Recommended” setup options, causing it to install automatically if users don’t manually deselect it. Is Giant Coupons Official Extension a Real Threat? While not as destructive as ransomware or banking trojans, Giant Coupons Official Extension still poses real risks.…
BeatBanker
BeatBanker is a dangerous Android malware that disguises itself as legitimate apps, giving attackers remote control of your device and access to sensitive data. Once installed, it can drain your battery, slow down your device, steal banking or cryptocurrency credentials, and secretly mine cryptocurrency. This guide explains how BeatBanker works, how it infects your phone, and what steps you can take to fully remove it. Threat TypeAndroid Banking Trojan / Crypto Miner / Remote Access MalwareDetection NamesHEUR:Trojan-Dropper.AndroidOS.BeatBanker, HEUR:Trojan-Dropper.AndroidOS.Banker.*SymptomsRapid battery drain, overheating, unknown apps installed, device slowdown, suspicious permissionsDamage & DistributionCryptocurrency mining, credential theft, crypto wallet manipulation, remote device control; spreads via fake app stores and malicious APK downloadsDanger LevelHighRemoval ToolSpyHunter How BeatBanker Gets Installed on Android BeatBanker infects devices primarily through fake app downloads. Attackers create websites that look like the official Google Play Store, tricking users into downloading a malicious APK. The malware often pretends to be popular apps or utilities to make the download appear safe. During installation, BeatBanker requests powerful permissions such as: Granting these permissions allows the malware to manipulate your device, install extra components, and hide its presence. It can also arrive via phishing pages that encourage sideloading apps outside the official marketplace. Users who unknowingly install these apps may have their phones compromised immediately. What BeatBanker Does on Your Phone Once active, BeatBanker begins multiple harmful actions: Even removing the app manually may not fully eliminate the malware, as it uses persistence techniques to reinstall itself or remain active in the background. Should You Factory Reset After BeatBanker? A factory reset is the most reliable way to remove BeatBanker. The malware uses tricks like running inaudible audio loops or abusing accessibility services to remain active even when you attempt to remove it manually. Before performing a reset: These steps ensure that all components of the malware are eliminated and your phone returns to safe operation. Conclusion BeatBanker is a multi-function Android malware that steals financial data, secretly mines cryptocurrency, and allows attackers remote access to your device. The malware spreads through fake app stores and sideloaded APK files, making careful app installation practices essential.…
Cormislen.com Ads
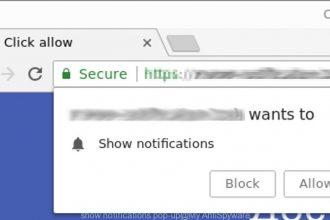
Cormislen.com is a rogue website designed to trick users into enabling browser notifications that later bombard them with intrusive ads and redirects. Once permission is granted, the site can push misleading alerts promoting scams, questionable software downloads, and potentially malicious websites. These notifications often appear even when the browser is closed, making the problem especially frustrating. While the site itself is not a traditional virus, it is strongly associated with notification spam and adware-driven redirects, which can expose users to serious security risks. Cormislen.com Adware Overview CategoryDetailsThreat TypeRogue website, push notification spam, adware-related redirectsDetection NamesNot widely classified (notification spam domain)SymptomsConstant pop-up ads, browser redirects, fake alerts, unwanted notificationsDamage & DistributionPrivacy risks, exposure to scams or malware, decreased browsing performanceDanger LevelMediumSpyHunter Linkhttps://www.enigmasoftware.com/products/spyhunter/?ref=ywuxmtf How Cormislen.com Affects Your Browser Cormislen.com abuses the browser notification feature, which legitimate sites use for updates or news alerts. Instead of delivering useful content, this page sends: The trick usually starts with a fake CAPTCHA verification page or a message telling you to click “Allow” to confirm you're not a robot or to access content. The moment you click the button, your browser grants permission for notifications. From that point forward, Cormislen.com can flood your desktop with ads linking to: Because notifications are handled by the browser itself, they appear even when you’re not actively visiting the site. Where Cormislen.com Comes From Most users never visit this site intentionally. Instead, they are redirected to it through several common sources: 1. Rogue Advertising Networks Certain shady websites display aggressive ads that automatically redirect visitors to pages like Cormislen.com. 2. Adware Installed on the System Potentially unwanted programs bundled with free software can modify browser settings and trigger unwanted redirects. 3. Misleading Pop-Ups Some pages display messages such as: These messages are simply traps designed to obtain notification permissions.…
Immigration Ransomware
Immigration ransomware is a dangerous malware that locks your files and demands payment to unlock them. Once it infects your system, it encrypts documents, photos, videos, and other important files, rendering them inaccessible. Victims are then presented with a ransom note instructing them to pay a fee, usually in cryptocurrency, to regain access to their data. Paying the ransom is risky—there’s no guarantee the attackers will provide a working decryption key. This guide explains how Immigration ransomware infects your system, what it does to your files, and practical steps to remove it and recover your data safely. Immigration Ransomware Threat Summary CategoryDetailsThreat TypeRansomware, File Locker, Crypto VirusEncrypted File ExtensionTypically appends a unique extension to encrypted filesRansom Note FilenameText file or on-screen instructionsEmail ContactProvided in the ransom noteDetection NamesFlagged by most security vendors as ransomwareSymptomsLocked files, renamed file extensions, ransom note displayedDamagePermanent file encryption, possible additional malware installationDistribution MethodsMalicious email attachments, pirated software, fake updates, infected downloadsDanger LevelHigh – encrypts personal and business files How Did I Get Infected With Immigration Ransomware? Immigration ransomware usually enters a system through everyday activities that seem harmless: Even a single mistake, like opening a malicious attachment, is enough for Immigration ransomware to start encrypting files. What Immigration Ransomware Does to Your Files After infection, Immigration ransomware immediately scans your system for valuable files, including: The malware encrypts these files, replacing the originals with unreadable versions and often changing file extensions. During this process, it also drops a ransom note and may alter your desktop wallpaper to display payment instructions. Once encryption is complete, your files are inaccessible unless you use backups or a decryption tool—paying the ransom is not guaranteed to work. Should You Be Worried About Immigration Ransomware? Yes. Immigration ransomware is a high-risk threat because it targets your most important files. Business data, personal photos, and work documents are all at risk. Important safety tips if infected: Ransom Note Dropped by Immigration Ransomware Immigration ransomware leaves a ransom note that explains the file encryption and provides instructions for payment. Typical contents include: Some versions may even offer to decrypt a single file as proof, which is a tactic to make victims trust the attackers. How to Remove Immigration Ransomware and Recover Files Taking these steps ensures your system is clean and reduces the risk of reinfection. Conclusion…
Kinerbum.com Ads
Kinerbum.com ads are aggressive pop-ups and browser notifications that interrupt browsing, display fake alerts, and push risky downloads. These ads often appear after users accidentally allow notifications from the site or install software bundled with adware. Once active, Kinerbum.com can flood your screen with unwanted ads, redirect you to suspicious websites, and promote potentially harmful software. Threat TypeAdware / Push Notification AdsDetection NamesAdware.Kinerbum, Browser:Adware.Kinerbum, Riskware.PushNotificationsSymptomsConstant pop-ups from Kinerbum.com, unexpected redirects, fake virus alerts, browser slowdownDamage & DistributionTracking browsing activity, redirecting to scam or unsafe websites, installing additional PUPsDanger LevelMediumRemoval ToolSpyHunter How Kinerbum.com Ads Interfere With Browsing Kinerbum.com primarily works by tricking users into allowing browser notifications. Once enabled, these notifications bypass your open tabs and appear directly on your desktop or mobile device. Users often see: These pop-ups continue even after closing the browser because they are delivered through your browser’s notification system. This can slow down your system, create a cluttered desktop experience, and increase the risk of accidentally clicking on malicious links. How Kinerbum.com Ads Get Installed Most people don’t visit Kinerbum.com directly. Common ways these ads appear include: The adware can install silently when users rush through software installations without reviewing the custom/advanced options, allowing the ad scripts to embed in browsers. Is Kinerbum.com Dangerous? Kinerbum.com is not a virus in the traditional sense, but it poses several risks: Even though the main goal is to generate advertising revenue, ignoring the problem can escalate the risk of malware exposure and system slowdowns. How to Remove Kinerbum.com Ads 1. Block Notifications from Kinerbum.com Google Chrome: Mozilla Firefox: Microsoft Edge:…
Unutcacer.com Ads
What Are Unutcacer.com Ads? Unutcacer.com ads are intrusive notifications and pop-ups that appear on your browser or desktop, often without clear permission. They’re designed to trick you into clicking links that may lead to scams, phishing pages, or websites offering suspicious downloads. While Unutcacer.com itself isn’t a virus, interacting with these ads can expose your system to threats. How Do You Start Seeing Unutcacer.com Ads? Most users encounter these ads after visiting websites that ask you to click “Allow” to continue to content, play a video, or pass a fake CAPTCHA. Once you click “Allow,” the site gains permission to send notifications directly to your browser or desktop. Even when your browser is closed, these notifications can appear, displaying fake warnings, fake updates, or special offers. Signs You Have Unutcacer.com Ads You might be affected if you notice: How to Remove Unutcacer.com Ads 1. Revoke Notification Permissions You need to remove Unutcacer.com from your browser’s notification permissions: Google Chrome Firefox Edge Safari (Mac) 2. Clear Browser Data Clearing cookies and cached data ensures leftover permissions and settings from Unutcacer.com are removed. 3. Check for Suspicious Extensions Some adware installs browser extensions without your knowledge. Open your extensions list and remove anything unfamiliar or recently added.…
Exallambous.com Ads
Warning: If your browser keeps showing pop-ups or notifications from exallambous.com, it’s not a normal alert. These ads are deceptive and can redirect you to unsafe websites if clicked. Acting fast will prevent further interruptions and potential exposure to scams. What Is Exallambous.com Ads? Exallambous.com is a browser-based ad service that tricks users into allowing notifications. It does not infect your computer like a traditional virus, but it can flood your screen with: Once your browser allows notifications, these ads appear at any time, even when you’re not visiting the site. How Did I Get These Ads? Most people accidentally give permission by clicking “Allow” on a prompt disguised as: These prompts are designed to look like legitimate website requests. Clicking “Allow” gives the site permission to send notifications directly to your device. Why Exallambous.com Ads Are a Problem Even though the site doesn’t install malware, the ads it sends can cause: Allowing these notifications also increases the risk of accidentally downloading actual malware from scam websites. How to Stop Exallambous.com Ads 1. Revoke Notification Permissions You need to remove exallambous.com from your browser’s Allowed Notifications list: Once removed, make sure to Block any future notification requests from unknown sites. 2. Close Suspicious Tabs Immediately close any browser tabs prompting you to allow notifications. These are often temporary but harmful windows. 3. Scan for Unwanted Programs Even though exallambous.com is not malware, interacting with its ads can expose you to adware or potentially unwanted programs. Running a full system scan with a trusted security tool ensures your device stays clean. How to Prevent These Ads in the Future…
Raptum Ransomware
Warning: Raptum ransomware encrypts your files and holds them hostage. Acting quickly can help prevent further damage and data loss. Raptum is a dangerous ransomware strain that locks your personal and work files, adds a unique extension to them (like .raptum46), and demands payment to restore access. Once it’s on your system, it spreads to connected drives, overwrites file access, and leaves a ransom note instructing you to pay to recover your data. 📌 Threat Summary Threat NameRaptum ransomwareThreat TypeRansomware, Crypto VirusEncrypted File Extension.raptum46 (number may vary)Ransom Note FilenameRECOVER_DATA.htmlCyber Criminal Contactrecovery2@salamati.vip, recovery2@amniyat.xyzDetection NamesAvast: MalwareX-gen, ESET‑NOD32: MedusaLocker variant, Microsoft: Win64/MedusaLockerSymptomsFiles renamed and inaccessible, desktop wallpaper changed, ransom note displayedDamage & DistributionEncrypts nearly all personal files; spread via email attachments, pirated apps, fake updates, malicious websitesIs Decryptor Available?❌ No free decryptor availableDanger Level🔥 High (risk of permanent data loss) How Did I Get Infected With Raptum Ransomware? Raptum typically infects systems through: Once installed, it starts encrypting files immediately, adding a .raptum## extension, and making them unusable without a decryption key. What Raptum Ransomware Does to Your Files Raptum ransomware: Even after removal of the ransomware itself, encrypted files remain locked unless you have backups or a decryptor. Should You Be Worried About Raptum Ransomware? Yes. Raptum is highly dangerous because: Immediate action is crucial to prevent further encryption and data loss. Ransom Note Dropped by Raptum Ransomware The ransom file RECOVER_DATA.html instructs victims to: These messages are designed to pressure you into paying…
Bestizatic.com Ads
Bestizatic.com ads are intrusive browser notifications that can disrupt your browsing, lead to scam sites, or trick you into installing unwanted software. If you’ve been seeing pop-ups or alerts from this site, it’s crucial to remove them quickly to protect your privacy and prevent further annoyance. 🧠 What Are Bestizatic.com Ads? Bestizatic.com ads are a type of push notification spam. They aren’t malware in the traditional sense, but they exploit your browser’s notification system. Once you grant permission, the site can send persistent pop-ups, fake alerts, and misleading offers directly to your desktop or browser—even when you’re not visiting the website. 🚨 How Bestizatic.com Ads End Up on Your Browser These notifications may link to fake system warnings, scam tech support sites, phishing pages, or downloads for unwanted programs. Even though the ads themselves don’t infect your system, interacting with them can expose you to real threats. 🛑 Are Bestizatic.com Ads Dangerous? The notifications themselves are not a virus, but they increase your exposure to scams and malicious content. Risks include: Even if nothing is downloaded immediately, these ads create a gateway for more serious threats if ignored. ✅ How to Remove Bestizatic.com Ads 1. Revoke Notification Permission in Your Browser Chrome (Desktop): Firefox: Edge: Safari (macOS): 2. Clear Browser Data Deleting cookies and cached files helps prevent automatic redirects back to Bestizatic.com. 3. Scan for Adware or Unwanted Programs Sometimes these notifications appear because adware or PUPs are installed on your system. Running a reputable anti-malware scan will find and remove any hidden threats.…
Copetring.com Ads
What Copetring.com Ads Are Copetring.com Ads are intrusive push notifications that appear on your computer or mobile device, often even when your browser is closed. They are triggered by websites that trick you into granting notification permissions. Once allowed, these ads can deliver unwanted pop-ups, fake alerts, or links to risky sites. This is not a traditional virus, but it behaves like adware — it disrupts your browsing and can expose you to scams or malware downloads. How Copetring.com Tricks Users The Copetring.com website uses deceptive prompts, often disguised as: Clicking Allow unknowingly gives the site permission to send notifications straight to your device. Once granted, it can display: The goal is to trick you into engaging with these ads, sometimes leading to malware infections or financial scams. Signs You’re Infected With Copetring.com Ads You may be affected if you notice: If these symptoms are happening, it’s usually because your browser gave Copetring.com permission to send notifications. How to Remove Copetring.com Ads 1. Revoke Notification Permissions The first step is removing the site’s ability to send notifications. Chrome (Windows/macOS): Firefox: Edge: Safari: Once done, the push notifications should stop immediately.…
MilfHookup.app
MilfHookup.app presents itself as a casual dating platform, but many users encounter aggressive advertising, fake profiles, and redirects rather than genuine matches. If you’re seeing this site unexpectedly, or you’re considering using it, it’s important to understand the risks and how to protect yourself. ⚠️ Why MilfHookup.app Can Be Risky Misleading Profiles and Messages The platform often uses automated accounts and messages to encourage subscriptions. Many interactions are not with real people, which can lead to wasted money or personal information being shared with third parties. Redirects and Pop-Ups If your browser keeps sending you to MilfHookup.app, it’s a strong sign that your device may have adware or potentially unwanted programs (PUPs) installed. These programs can generate constant pop-ups, redirect you to risky sites, and even slow down your device. Privacy Concerns Sites like this can collect emails, phone numbers, or payment information. If you’ve already entered any personal data, you could be targeted with spam, scam messages, or unwanted subscription charges. 🧹 How to Protect Yourself from MilfHookup.app 1. Check for Adware or PUPs Run a full antivirus or anti-malware scan to detect and remove adware or unwanted programs that may be causing redirects. 2. Inspect Your Browser Remove suspicious extensions or add-ons, clear your cache, and reset your browser settings if redirects continue. 3. Avoid Sharing Personal Information Never provide emails, phone numbers, or financial details on platforms that you cannot trust. 4. Consider Using Safe Alternatives Stick to reputable dating apps with verified profiles. Avoid sites that rely on aggressive marketing tactics or automated messages. 🛑 Key Takeaways 💡 Action Steps
Hamstep.com
Warning: Persistent pop-ups, redirects, and fake notifications can expose your system to scams and unwanted content. The Hamstep.com Pop‑ups Virus is a type of adware that hijacks your browser notifications to push intrusive ads, fake alerts, and redirects. It tricks users into granting permission for notifications through deceptive prompts, often claiming you need to click “Allow” to verify you are human. Once permission is given, your browser can flood you with unwanted messages, even when you’re not actively browsing. How Hamstep.com Pop‑ups Appear These pop-ups are designed to look legitimate, but their real goal is to generate ad revenue by pushing unwanted notifications to your system. Signs Your System Is Affected Even though it’s not a traditional virus, the problem is serious because these pop-ups can lead to scams, phishing pages, or even malware if clicked. How to Stop Hamstep.com Pop‑ups 1. Revoke Notification Permissions To cut off the pop-ups, remove Hamstep.com from your browser notifications: Chrome / Edge / Firefox: This immediately stops new pop-ups from appearing. 2. Remove Suspicious Browser Extensions 3. Scan Your System for Adware or PUPs While Hamstep.com itself works through the browser, other potentially unwanted programs may be installed that trigger similar behavior. Use a trusted anti-malware tool to scan and remove these threats. 4. Clear Cache and Reset Your Browser 5. Avoid Risky Sites Why You Should Act Quickly…
Cynovira.com Ads
Cynovira.com ads are intrusive browser notifications and redirects generated by a deceptive website that tricks users into allowing push notifications. Once…
PromptSpy
PromptSpy is an advanced Android spyware that uses generative AI to help it stay active on infected devices. Once installed, it…
BoryptGrab Stealer
BoryptGrab Stealer is a dangerous data‑stealing malware targeting Windows systems. It spreads through fake software downloads and is designed to harvest…
Pornhits.com
Pornhits.com redirects can expose your browser to intrusive ads, tracking scripts, and potentially unwanted programs (PUPs). If your browser suddenly opens…
Valrelio.co.in Scam
Valrelio.co.in is a deceptive website designed to trick users into enabling malicious browser notifications that can lead to scams, malware,…
iScans Fake Crypto Tracker
The iScans Fake Crypto Tracker virus is a malicious crypto-themed scam platform designed to trick users into believing they have cryptocurrency…
QuickLens – Search Screen with Google Lens Virus
QuickLens – Search Screen with Google Lens is a malicious browser extension that disguises itself as a helpful tool for searching…
Euresupply.com
Euresupply.com is a suspicious website frequently linked to scam activity, deceptive online stores, and aggressive browser redirects. If your browser keeps…
GhostForm RAT
GhostForm RAT is a dangerous Remote Access Trojan (RAT) designed to secretly control infected computers, steal sensitive information, and allow attackers…
Freieporno.com
Freieporno.com is commonly reported by users searching for terms like “Freieporno.com virus removal,” “Freieporno.com redirect virus,” or “Is Freieporno.com a virus?” If you’re seeing constant…
Prisporbinagena.com
Prisporbinagena.com virus removal is a high-intent search query — and if you’re here, you’re likely dealing with intrusive pop-ups, browser redirects,…
Ribaki.org
Ribaki.org browser hijacker alert: If Ribaki.org keeps redirecting your browser, pushing pop-ups, or replacing your homepage, your system is likely affected…
Fake Tari XTM Airdrop Scam
The Fake Tari XTM Airdrop Scam is a high-risk cryptocurrency phishing threat targeting users across Windows and macOS systems. This…
“Chargeback Invoice” Scam
The Chargeback Invoice virus is a phishing email scam targeting Windows users. It disguises itself as a legitimate invoice attachment and tricks recipients into…
ZETARINK
Written by cybersecurity researcher | Last Updated: March 2026 If your computer has been affected by ZETARINK ransomware, this guide will…
MaskGrimStealer
MaskGrimStealer is a real Windows credential‑stealing trojan that targets stored passwords, browser data, cryptocurrency wallets, and other sensitive credentials. MaskGrimStealer malware quietly harvests…
cPanel Roundcube
If you’ve received a message claiming that your email needs verification through cPanel Roundcube, you may be dealing with a phishing…
Reynolds Ransomware
If your computer is infected with Reynolds ransomware, you are dealing with a real, file-encrypting threat that targets Windows operating systems. This…
DealSearchPro.com
If you’ve noticed your browser constantly redirecting to DealSearchPro.com, your system is infected with a browser hijacker. This threat modifies your homepage,…
Witch Virus
If your computer has been affected by Witch ransomware, you’re dealing with a legitimate and high-risk malware threat targeting Windows systems.…
Ad Dimmer
If you’re searching for Ad Dimmer virus removal, it’s important to understand that this is a real adware threat affecting Windows systems.…
“cPanel System Maintenance” Email Scam
The cPanel System Maintenance Email Scam is a real threat targeting email users on Windows and macOS systems. Classified as a phishing…
KarstoRAT Trojan
KarstoRAT is a remote access Trojan (RAT) that targets Windows systems, giving attackers unauthorized control over your computer. This malware operates silently, harvesting…
Osa Virus
Osa virus is a ransomware threat that targets Windows operating systems, encrypting personal and business files to demand a ransom.…
Splumatorwrin.com
Splumatorwrin.com is a browser-based notification malware that targets Windows and macOS systems, misleading users into allowing persistent notifications that deliver…
Locate.webnavigatorhub.com
If your browser keeps redirecting to Locate.webnavigatorhub.com, your system is likely infected with a browser hijacker affecting Windows or Mac operating systems. This…
Qaventro.com
Warning: Qaventro.com is a high-risk cryptocurrency platform that may compromise your personal information, financial data, or even your computer. If you’ve…
assets.allegrostatic.com Pop-Ups
Warning: Persistent pop-ups from assets.allegrostatic.com can indicate adware or a browser hijacker infection that affects your browsing experience and privacy. If…
How to Deal With Nhanrobux.fun – Scam Breakdown & Safety Tips
Fake Robux generator scam targeting Roblox players Nhanrobux.fun is a fraudulent website that promises free Robux for Roblox players. The site claims…
SURXRAT
SURXRAT is a dangerous Android Remote Access Trojan (RAT) that gives attackers near-total control over infected devices. It steals sensitive data,…
Trojanized Teramind Software
Threat: Trojanized Teramind Software – malicious remote access and monitoring toolWarning: This trojanized software silently installs a remote monitoring agent that can…