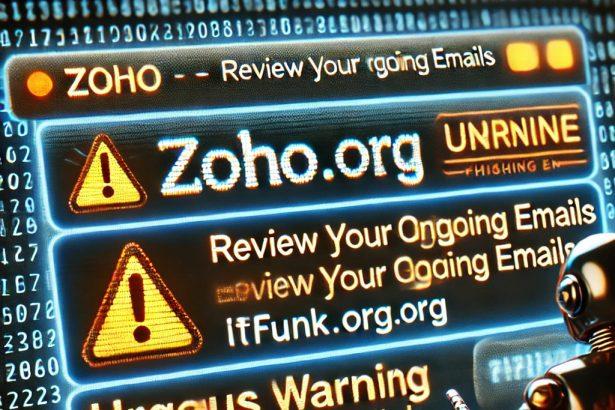
The “Zoho – Review Your Outgoing Emails” scam is a phishing attack disguised as a security notification from Zoho Mail. Scammers use such emails to lure victims into providing sensitive credentials on a fake web page.
Threat Overview
This table summarizes the critical details of the “Zoho – Review Your Outgoing Emails” scam:
| Attribute | Details |
|---|---|
| Name | Zoho – Review Your Outgoing Emails Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Outgoing emails have been rejected |
| Disguise | Notification from Zoho |
| Symptoms | Generic greeting, urgent language, suspicious links, grammatical errors |
| Distribution Methods | Deceptive emails, rogue pop-up ads, search engine poisoning, misspelled domains |
| Damage | Loss of sensitive information, monetary loss, identity theft |
| Danger Level | High |
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!
Details of the Scam
The scam begins with an email claiming to alert users about rejected outgoing emails. It uses an urgent tone and a provided link to lead recipients to a phishing website. The fake site mimics Zoho’s official login page, requesting the victim’s email or mobile number and password.
What Happens If You Fall for It?
- Account Breach: Scammers can access email, social media, or financial accounts linked to the stolen credentials.
- Identity Theft: Misuse of private data to commit fraud or sell it on the dark web.
- Financial Loss: Funds could be transferred from linked accounts.
- Further Phishing: Your contacts might receive phishing emails from your compromised account.
Removal Guide
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!
If you suspect your system is compromised due to phishing links or malware, use a reputable anti-malware tool like SpyHunter to clean it. Below are the steps:
Step 1: Disconnect from the Internet
Prevent additional data theft or malware activity by disconnecting your device.
Step 2: Use SpyHunter to Scan Your System
- Download and install SpyHunter.
- Launch the tool and select the System Scan option.
- SpyHunter will identify and list malicious files or programs, including potential phishing-related malware.
- Click Remove to eliminate detected threats.
Step 3: Secure Your Accounts
- Change Your Passwords: Immediately update passwords for your Zoho account and any associated accounts.
- Enable Two-Factor Authentication: Add an extra layer of security to prevent unauthorized access.
Step 4: Monitor for Suspicious Activity
Check your accounts for unauthorized transactions or changes. If any are detected, report them to the relevant service provider.
Preventing Future Infections
- Verify Email Authenticity
- Look for grammatical errors or inconsistencies.
- Avoid clicking on links without verifying their origin.
- Check sender email addresses carefully for misspellings.
- Secure Your Devices
- Use trusted antivirus software and keep it updated.
- Regularly update your operating system and applications to patch vulnerabilities.
- Educate Yourself
- Learn to recognize phishing techniques.
- Stay informed about current scams targeting users.
- Employ Email Filters: Use spam filters to detect and block suspicious emails.
- Avoid Public Wi-Fi: Avoid accessing sensitive accounts when connected to unsecured networks.
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!