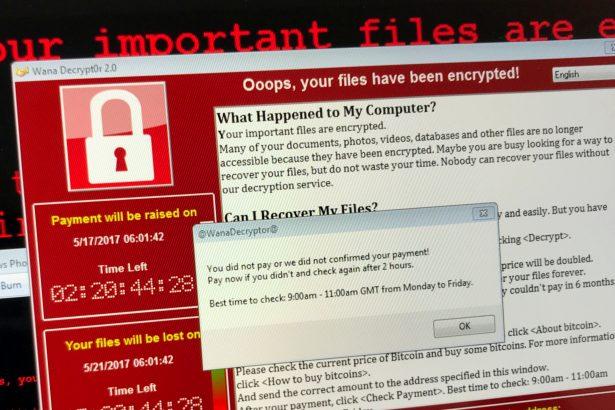
Nnice ransomware is a malicious program designed to encrypt files and extort victims by demanding payment for file decryption. This ransomware appends the “.nnice” extension to affected files and leaves a ransom note (“read_me.txt”) on the desktop, informing the victim about the encryption and instructing them to contact the attacker for a decryption tool. Here’s a detailed breakdown of the Nnice ransomware, along with actionable advice for its removal and future prevention.
Threat Summary
| Attribute | Details |
|---|---|
| Name | Nnice Ransomware |
| Threat Type | Ransomware, Crypto Virus, File Locker |
| Encrypted File Extension | .nnice |
| Ransom Note File Name | read_me.txt |
| Associated Email Address | maxfromhim@gmail.com |
| Detection Names | Avast: Win32:RansomX-gen [Ransom], Combo Cleaner: Gen:Heur.Ransom.Imps.3, ESET-NOD32: A Variant Of MSIL/Filecoder.Chaos.A, Microsoft: Ransom:MSIL/FileCoder.AD!MTB |
| Symptoms of Infection | Inaccessible files with “.nnice” extension, ransom note displayed, desktop wallpaper changed, and ransom demanded (usually in cryptocurrency). |
| Damage | Permanent encryption of files, potential installation of other malware or password stealers. |
| Distribution Methods | Phishing emails, malicious attachments, torrent websites, compromised advertisements, and infected USB drives. |
| Danger Level | High |
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!
Ransom Note Details
The ransom note, named read_me.txt, states:
"Hello, all your files have been encrypted and you can't decrypt this without the special file. Contact: maxfromhim@gmail.com."
Additionally, the desktop wallpaper is changed to display a vulgar ransom demand, emphasizing the attacker’s insistence on payment.
How Nnice Ransomware Spreads
- Phishing Emails: Fraudulent emails containing malicious attachments or links are the most common vector.
- Malicious Websites: Visiting compromised or fake websites can trigger ransomware downloads.
- Pirated Software: Cracks, keygens, or illegal software downloads often carry ransomware payloads.
- Exploited Vulnerabilities: Outdated software or operating systems are prime targets for attackers.
- Malvertising: Clicking on malicious ads can silently deliver ransomware to your system.
- Infected USB Drives: Using compromised external devices can also spread ransomware.
Why You Should Not Pay the Ransom
Paying the ransom is not recommended because:
- No Guarantee: Attackers may not provide the decryption tool even after payment.
- Encourages Crime: Payment incentivizes cybercriminals to continue their activities.
- Potential Risks: Decryption tools from attackers might contain additional malware.
Steps to Remove Nnice Ransomware
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!
SpyHunter is a powerful anti-malware tool capable of detecting and removing ransomware like Nnice. Follow these steps:
Download and Install SpyHunter
- Download the software.
- Install it by following the on-screen instructions.
Run a Full System Scan
- Open SpyHunter and initiate a full scan.
- The software will detect Nnice ransomware and any associated threats.
Remove Detected Threats
Click on “Fix Threats” to remove Nnice ransomware and any additional malware.
Restore Encrypted Files
Unfortunately, SpyHunter does not decrypt files. You may attempt to restore files from backups or use third-party decryption tools if available.
Preventing Future Ransomware Infections
- Keep Software Updated: Regularly update your operating system and software to patch vulnerabilities.
- Use Reputable Security Software: Install and maintain robust antivirus and anti-malware programs like SpyHunter.
- Avoid Suspicious Emails: Do not open attachments or click on links in emails from unknown senders.
- Download from Trusted Sources: Avoid downloading software from unofficial or P2P sources.
- Backup Data Regularly: Maintain secure backups on an external drive or cloud storage.
- Enable Firewall Protection: Use a firewall to monitor and block unauthorized access.
- Educate Yourself: Stay informed about the latest cybersecurity threats and best practices.
Conclusion
Nnice ransomware is a serious cyber threat that encrypts files and demands payment for their restoration. Removing it quickly using SpyHunter is critical to minimize damage. By adhering to cybersecurity best practices, users can protect themselves from future infections. Prevention is the most effective defense against ransomware, so take proactive measures today to safeguard your digital assets.
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!