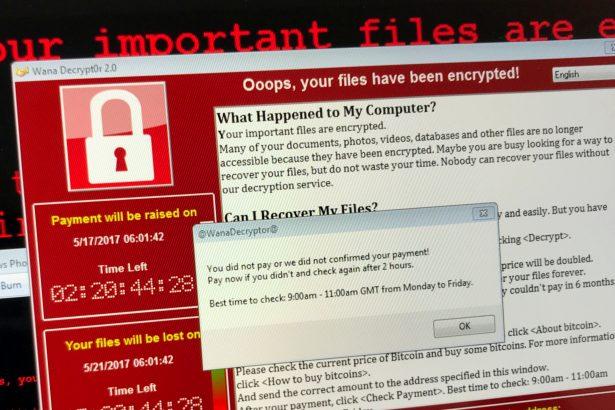
Nitrogen ransomware is a malicious software designed to encrypt files on infected systems, rendering them inaccessible without a decryption key. Cybercriminals use Nitrogen ransomware to target businesses across various sectors, including construction, financial services, manufacturing, and technology. Once it infiltrates a system, it appends the “.NBA” extension to encrypted files and creates a ransom note named “readme.txt.”
- Key Characteristics of Nitrogen Ransomware
- Scan Your Computer for Free with SpyHunter
- The Ransom Note: A Closer Look
- How Nitrogen Ransomware Infiltrates Systems
- Symptoms of Nitrogen Ransomware Infection
- Why You Should Not Pay the Ransom
- Removing Nitrogen Ransomware
- Preventing Future Ransomware Infections
- Conclusion
- Text in the Ransom Note
For instance, files such as “1.jpg” and “2.png” are renamed to “1.jpg.NBA” and “2.png.NBA,” respectively, indicating they are no longer accessible. Victims are informed through the ransom note that their corporate networks have been encrypted, and confidential data has been stolen. The attackers threaten to publish this data if their demands are not met, further adding pressure by suggesting that stolen information could be sold to scammers targeting the victim’s clients and employees.
Key Characteristics of Nitrogen Ransomware
- File Extension: .NBA
- Ransom Note: readme.txt
- Cybercriminal Contact: qTox messaging platform
- Primary Target Sectors: Construction, financial services, manufacturing, technology
- Anti-Analysis Techniques: Debugger detection, virtual machine detection, code obfuscation
- System Reconnaissance: Enumeration of PE sections and collection of detailed system information
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!
The Ransom Note: A Closer Look
The Nitrogen ransom note provides detailed instructions for victims to contact the attackers via the qTox messaging platform. The note includes:
- A warning that confidential data has been stolen and encrypted.
- Threats of public data exposure and further attacks if contact is not made.
- Detailed steps for setting up qTox and sending a friend request to the attackers.
It explicitly advises victims not to rename or alter any encrypted files, as doing so could cause permanent data loss.
How Nitrogen Ransomware Infiltrates Systems
Nitrogen ransomware is typically distributed through the following methods:
- Malicious Email Attachments: Often containing macro-enabled documents or executables.
- Compromised Websites: Redirecting users to exploit kits.
- Pirated Software and Keygens: Frequently bundled with ransomware payloads.
- Malicious Ads: Leading to downloads of infected files.
- USB Drives and P2P Networks: Acting as additional vectors for spreading the malware.
Symptoms of Nitrogen Ransomware Infection
- Files are inaccessible and have the ".NBA" extension.
- The presence of a ransom note (readme.txt).
- Messages demanding payment in cryptocurrency for file decryption.
- Possible installation of additional malware, such as password stealers.
Why You Should Not Pay the Ransom
Paying the ransom is highly discouraged for several reasons:
- No Guarantee of Recovery: Cybercriminals may not provide the decryption key even after payment.
- Encourages Further Attacks: Paying ransoms motivates attackers to continue their operations.
- Risk of Data Exposure: Attackers may still sell or leak stolen data.
Removing Nitrogen Ransomware
Removing ransomware like Nitrogen requires a robust anti-malware tool. SpyHunter is a trusted solution designed to detect and eliminate ransomware and related threats effectively.
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!
- Boot in Safe Mode:
- Restart your computer and press F8 or the appropriate key to enter Advanced Boot Options.
- Select "Safe Mode with Networking."
- Download SpyHunter: Install and launch the program.
- Run a Full System Scan:
- Click on "Scan Computer Now."
- Allow SpyHunter to detect all threats, including Nitrogen ransomware.
- Remove Detected Threats: Review the scan results and click "Fix Threats" to remove ransomware and associated files.
- Restart Your Computer: After removal, restart your system in normal mode.
Preventing Future Ransomware Infections
- Regular Backups: Maintain up-to-date backups on external or cloud storage.
- Email Caution: Avoid opening attachments or clicking links in unsolicited emails.
- Use Trusted Software: Only download software from reputable sources.
- Update Regularly: Keep your operating system and applications updated with the latest security patches.
- Install Antivirus Software: Use a reliable antivirus program and enable real-time protection.
- Educate Users: Conduct cybersecurity training for employees to recognize phishing attempts and other malicious activities.
Conclusion
Nitrogen ransomware poses a severe threat to businesses and individuals, encrypting valuable data and demanding payment for its release. While the consequences can be devastating, removing the ransomware with tools like SpyHunter and following preventive measures can mitigate risks. Regular backups, updated security software, and cautious online behavior are essential for defending against such attacks.
Text in the Ransom Note
What's happened?
Your corporate network has been encrypted. And that’s not all - we studied and downloaded a lot of your data, many of them have confidential status.
If you ignore this incident, we will ensure that your confidential data is widely available to the public. We will make sure that your clients and partners know about everything, and attacks will continue. Some of the data will be sold to scammers who will attack your clients and employees.
What's next?
You must contact us via qTox to make a deal. To install qTox follow the following instructions:
1. Follow the link to the official release and download the installation file.
hxxps://github.com/qTox/qTox/releases/download/v1.17.6/setup-qtox-x86_64-release.exe
2. Open and install setup-qtox-x86_64-release.exe
3. Double-click the qTox shortcut on your desktop.
4. In the username field, enter the name of your company.
5. Create your password and enter it in the password field.
6. Enter your password again in the confirm field
7. Click the "Create Profile" button.
8. In the Add Friends window, in the ToxID field, enter this:
74773DBD4085BA39A1643CFA561488124771B E839961793DA10245560E1F2D3A3DBD566445E8
then click the "Send friend request" button
9. Wait for technical support to contact you.
Advantages of dealing with us:
1. We will not mention this incident.
2. You will receive a recovery tool for all your systems that have been encrypted.
3. We guarantee that there will be no data leakage and will delete all your data from our servers.
4. We will provide a security report and give advice on how to prevent similar attacks in the future.
5. We will never attack you again.
What not to do:
Do not attempt to change or rename any files - this will render them unrecoverable. Do not make any changes until you receive the decryption tool to avoid permanent data damage.