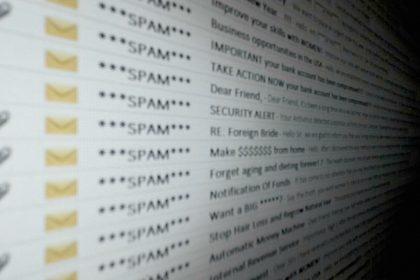
Aruba IT Email Scam: A Comprehensive Malware Removal Guide
Phishing scams are deceptive tactics used by cybercriminals to manipulate individuals into…
XIXTEXRZ Ransomware: Threats, Symptoms, and Removal Guide
Ransomware is a type of malicious software designed to deny access to…
Skotes.exe Virus: Actions, Consequences, and Removal Guide
New threats emerge daily, and one of the most concerning is the…
Hkbsse.exe Virus: Threats, Removal, and Prevention
Cyber threats are becoming increasingly sophisticated, posing serious risks to both personal…
Behavior.Win32.AMSI.Patch: A Growing Cyber Threat
Malware like Behavior.Win32.AMSI.Patch poses significant threats to both personal and organizational systems.…
Behavior:Win32/WDBlockFirewallRule.P – A Cyber Threat to Your Security
In today’s digital landscape, the rise of cyber threats like Behavior:Win32/WDBlockFirewallRule.P poses…
InstantQuest Browser Extension Malware
The InstantQuest browser extension is categorized as potentially unwanted software (PUP) and…
ElonMuskIsGreedy Ransomware: A Malicious Threat
Ransomware is a formidable form of malware that has increasingly become a…
MRDark101 Ransomware: Threats, Symptoms, and Removal
Ransomware is a malicious form of software that threatens to encrypt a…
Root (MedusaLocker) Ransomware: A Threat to Your System
Ransomware is a form of malware designed to encrypt a victim’s files,…