FadBlock: Understanding the Trojan Horse Threat
If you've noticed peculiar behavior on your computer, such as sluggishness, unresponsive applications, or unexpected warnings from your antivirus software,…
Onlypcflow.co.in: Battling the Browser Hijacker Onslaught
If you've found your web browser under the control of an unwelcome entity called Onlypcflow.co.in, your online experience is likely…
Brob.co.in: Battling the Browser Hijacking Nuisance
In the ever-evolving landscape of cybersecurity threats, browser hijackers like Brob.co.in have become a persistent nuisance, infiltrating systems and transforming…
Clampi Virus: Unveiling the Crafty Trojan Threat
In the intricate realm of cyber threats, Clampi stands out as a crafty Trojan that silently infiltrates systems, employing advanced…
7899.guru Annoying Pop-ups: A Comprehensive Guide
Tired of dealing with those persistent pop-up ads from 7899.guru? It's time to take decisive action. Our guide is here…
Caraesale.shop Annoying Pop-ups: A Comprehensive Guide
Are you tired of the persistent pop-up ads from Caraesale.shop disrupting your online experience? It's time to take action and…
SSJ4 Virus: A Browser Hijacker on the Prowl
SSJ4, also identified as ssj4.io and ssj4.main, has emerged as a persistent browser hijacker causing unwanted redirects on the Chrome…
Unveiling the Disruption Caused by Abelectivirean.com
Abelectivirean.com has gained notoriety for its intrusive push notifications and redirect loops, causing unwelcome disruptions for users. This article delves…
Unmasking the Intrusive Nature of Jastugoa.top
Jastugoa.top has emerged as a disruptive website known for its annoying pop-ups and notifications, raising concerns about potential privacy compromises.…
Unveiling the Intrusive Nature of Inetaispially.com
Inetaispially.com has emerged as a notorious website known for its disruptive push notifications and redirect loops, posing a significant threat…
Mispadu Trojan Exploits Windows SmartScreen Flaw: A Threat to Mexican Users
The cybersecurity landscape has witnessed the resurgence of the Mispadu banking Trojan, employing a patched Windows SmartScreen security bypass flaw…
LDHY Ransomware: A Menace from the STOP/Djvu Ransomware Lineage
Amidst the expansive landscape of cyber threats, LDHY Ransomware emerges as a sinister iteration within the notorious STOP/Djvu Ransomware family.…
Networkpcigniter.com: A Rogue Webpage Exploiting Deceptive Content and Push Notification Spam
In the realm of cybersecurity, rogue webpages like networkpcigniter.com pose a significant threat to online users. Through deceptive content and…
Totalnicenewz.com – Navigating the Hazards of Rogue Webpages
In the ever-evolving landscape of online threats, rogue webpages like totalnicenewz.com have emerged as conduits for various cyber risks. Discovered…
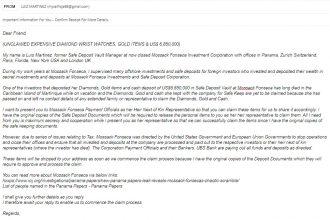
“Unclaimed Expensive Goods” Email Scam: A Deceptive Scheme Exploiting Mossack Fonseca Connection
In the realm of cyber threats, phishing scams persist as a prevalent danger, with attackers deploying cunning tactics to exploit…
“KYC (Know Your Customer) Verification” Email Scam: A Cryptocurrency Threat
In the ever-evolving landscape of cyber threats, scams targeting cryptocurrency users continue to rise. The "KYC (Know Your Customer) Verification"…
“BitDogs Mint Free” Scam: A Crypto-Draining Deception
In the dynamic world of cryptocurrencies and NFTs (Non-Fungible Tokens), scammers are employing sophisticated tactics to deceive users and drain…
MethodOnline: The Adware Intruder on Your Mac
In the ever-evolving landscape of cyber threats, adware continues to be a persistent menace. MethodOnline, a recent addition to the…
DataControl: Navigating the Adware Menace
In the realm of cybersecurity, threats evolve, and among them, advertising-supported applications like DataControl wield intrusive tactics. This article aims…
LPER Ransomware: A Menace from the STOP/Djvu Ransomware Lineage
Amidst the expansive landscape of cyber threats, LPER Ransomware emerges as a sinister iteration within the notorious STOP/Djvu Ransomware family.…
How Do I Deal with the ESSY Ransomware Infection?
ESSY Ransomware is yet another malware strain that is a part of the prolific STOP/Djvu Ransomware family. Like other similar…
Onepcseries.co.in: A Browser Hijacker Disruption
When your web browser becomes a victim of a browser hijacker like Onepcseries.co.in, it can lead to a series of…
TheHiddenObjectShow Adware on Mac: Unmasking the Threat
TheHiddenObjectShow has emerged as a potent adware threat targeting Mac users, causing a surge in intrusive pop-ups, unexpected redirects, and…
PixelMegabyte: Unwanted Adware on Your Mac
In the ever-evolving landscape of online threats, PixelMegabyte has emerged as a potential menace, classified as adware. This application raises…
PrivateLoader: Unveiling the Elusive Threat
In the perilous realm of cybersecurity, PrivateLoader stands out as a sophisticated and adaptable malware, categorized as a loader with…
VajraSpy Android Malware: A Threat to Your Privacy
In the ever-evolving landscape of cyber threats, VajraSpy stands out as a formidable adversary, specifically designed for targeted espionage on…
“VisionCoordinator Will Damage Your Computer” on Mac – Removal
Mac users encountering the threat of VisionCoordinator need to act promptly to safeguard their systems. This guide is tailored to…
OfficerValue Will Damage Your Computer Mac – Removal: A Comprehensive Guide
If you find yourself encountering the ominous warning "OfficerValue will damage your computer" on your Mac, immediate action is necessary…
CVE-2022-48618: Apple Flaw in macOS, iOS Actively Exploited
In a recent revelation, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has identified and added a high-severity flaw to…
UNC4990 Threat Group: Exploiting USB Devices and Legitimate Platforms
In a recent revelation, cybersecurity firm Mandiant has exposed the activities of a financially motivated threat actor known as UNC4990.…
Re-captha-version-3-21.icu Browser Hijacker: A Comprehensive Guide
The online realm, while brimming with opportunities and information, is not without its pitfalls. Enter Re-captha-version-3-21.icu, a bothersome browser hijacker…
1E3mVbLSLLUgdmrp8GV5RRu1Qz5FkWs4rJ Bitcoin Email Scam
In the vast landscape of cyber threats, the 1E3mVbLSLLUgdmrp8GV5RRu1Qz5FkWs4rJ Bitcoin email scam has emerged as a deceptive and intimidating scheme.…
“Yamaha Baby Grand Piano” Email Scam
In the realm of cyber threats, scammers often employ various tactics to trick unsuspecting individuals, and one such deceptive scheme…
“Claim Manta” Cryptocurrency Giveaway Scam
In the ever-evolving landscape of online scams, a new threat has emerged— the "Claim Manta" cryptocurrency giveaway scam. This deceptive…
Dx31 Ransomware: Unraveling the Threat and Protecting Your Data
In a recent inspection of malware samples submitted to VirusTotal, a new ransomware named Dx31 has been identified as part…
StandartSkill Adware: Unwanted Ads and Privacy Risks
StandartSkill, upon detailed examination, has been identified as adware, presenting users with intrusive advertisements and potential privacy risks. This article…
Unharmonious.app: Adware Threat Analysis and Removal Guide
Unharmonious.app has been identified as advertising-supported software (adware) belonging to the Pirrit malware family. Discovered during an investigation of new…
CVE-2023-6246: GNU C Flaw Exposes Linux to Local Privilege Escalation
A critical security vulnerability, tracked as CVE-2023-6246, has been disclosed in the GNU C library (glibc), raising significant concerns in…
Critical File Writing Vulnerability (CVE-2024-0402) in GitLab: A High-Risk Flaw
A critical file writing vulnerability, identified as CVE-2024-0402, has been uncovered in GitLab CE/EE, impacting versions ranging from 16.0 to…
TypicalSource on Mac: Unveiling the Adware Threat
If your Mac is currently grappling with the threat of TypicalSource, swift action is imperative. This guide is tailored to…
SystemDesignMarket Mac Adware: Unveiling the Threat
For Mac users facing the intrusion of SystemDesignMarket, prompt action is imperative. This guide is meticulously crafted to aid users…
ExtendedOperation Adware on Mac: Unveiling the Threat
If you're facing the menace of ExtendedOperation on your Mac, swift action is imperative. This comprehensive guide is tailored to…
BounceTopics Adware: Unmasking the Threat
BounceTopics, identified as an adware-type application from the AdLoad malware family, poses a significant threat by delivering intrusive advertisement campaigns.…
RadioDiskInput Adware: Protecting Against Intrusive Ads
In recent investigations, cybersecurity experts have unveiled the RadioDiskInput application, operating as adware with the potential to compromise user information.…
AdjustableIndexer: Adware Lurking in the Shadows
The cybersecurity landscape continually evolves, and with it, the emergence of adware threatens the privacy and security of users. One…
“FTX Customer Claims” Scam: Protecting Your Cryptocurrency
In the vast realm of cyberspace, scammers are relentless in their pursuit of deceiving individuals and pilfering cryptocurrency. The "FTX…
ChallengeDiscovery: The Adware Onslaught
In the realm of cyber threats, ChallengeDiscovery has surfaced as a new adversary, revealing its identity as adware within the…
QuestDevice: Adware Intrusion on Mac
QuestDevice has emerged as a problematic application, marked by its intrusive advertisement tactics, classifying it as adware. Beyond bombarding users…
Browser Default: A Browser-Hijacking Nuisance on Mac
Browser Default, a potentially unwanted add-on infiltrating popular browsers such as Safari, Firefox, and Chrome, disrupts user experience by altering…
Notifzone.com: A Push Notification Peril
Have you encountered the vexing Notifzone.com and its persistent push notifications, inducing redirect loops? This article delves into the dubious…