CyberVolk Ransomware: Removing the Cyber Threat
Cybervolk ransomware is a formidable cyber threat that encrypts files on the…
Understanding and Removing the UltimateBackup Virus: A Comprehensive Guide
The UltimateBackup virus is a newly identified cyber threat that has been…
Xfun Ransomware: A Comprehensive Removal Guide & Prevention Tips
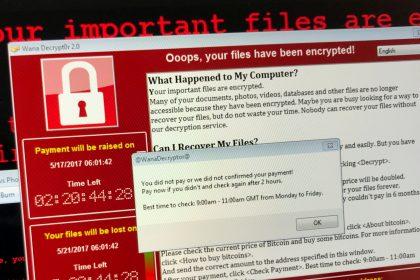
Ransomware has become one of the most formidable cyber threats of our…
RafelRAT: Understanding the Cyber Threat and How to Defend Against It
RafelRAT is a sophisticated Remote Access Trojan (RAT) that poses a significant…
Understanding and Removing the Trojan.Win32.Mywife Virus
The Trojan.Win32.Mywife virus stands out as a particularly insidious malware. Known for…
Zonix Ransomware: Understanding the Threat and How to Protect Your Systems
Ransomware attacks have become increasingly prevalent, posing significant threats to individuals and…
Understanding and Removing HardDriveThread Malware
The emergence of new malware strains continues to pose risks to individuals…
SRC Ransomware: A Comprehensive Guide to Detection, Removal, and Prevention
SRC Ransomware is a pernicious cyber threat that encrypts files on an…
Opix Ransomware: A Comprehensive Guide to Understanding, Removing, and Preventing This Cyber Threat
Ransomware continues to be one of the most formidable challenges. Among the…
Vidar Malware: A Stealthy Cyber Threat
Vidar malware stands out as a particularly insidious menace. Named after the…