PlayBoy LOCKER Ransomware: Comprehensive Removal and Prevention Guide
PlayBoy LOCKER is a highly dangerous ransomware that encrypts your files and…
Core (Makop) Ransomware: A Guide to Removal and Prevention
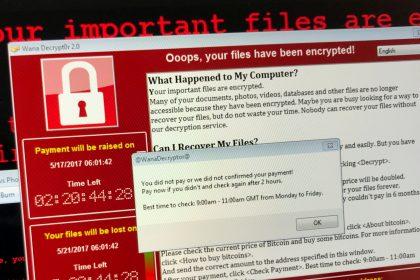
Ransomware remains one of the most persistent and damaging cyber threats. One…
V (Dharma) Ransomware: Analysis and Removal Guide
Understanding V (Dharma) Ransomware V is a ransomware variant belonging to the…
BlackLock Ransomware: A Analysis and Removal Guide
BlackLock is a ransomware-type virus that encrypts files and demands ransoms for…
Hunter Ransomware: A New Variant of Prince Ransomware – Removal & Prevention Guide
A new ransomware threat named Hunter has emerged, encrypting victims’ files and…
Hitler_77777 Ransomware: Analysis and Removal Guide
The Hitler_77777 ransomware is a dangerous cryptovirus identical to TRUST FILES ransomware.…
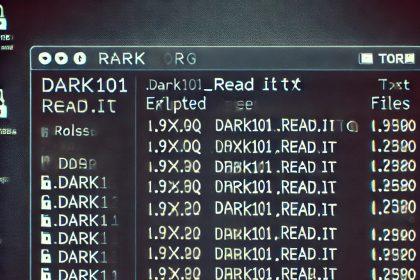
Dark 101 Ransomware: A Detailed Threat Analysis and Removal Guide
Dark 101 is a ransomware-type malware based on the Chaos framework, recently…
Helldown Ransomware Removal
Helldown is an aggressive ransomware strain first identified in August 2024. It…
Annoy Ransomware: Comprehensive Removal Guide & Prevention Tips
Have your files been locked by the Annoy Ransomware virus? This insidious…