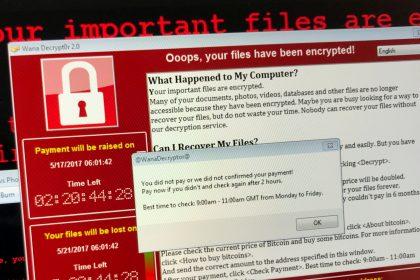
Interlock Ransomware: Detection, Removal, and Prevention
Ransomware is a malicious type of malware designed to encrypt files on…
Nyxe Ransomware: Threats, Symptoms, and Removal Guide
Ransomware is a type of malicious software designed to block access to…
Colony Ransomware: A Comprehensive Threat Overview and Removal Guide
Ransomware is one of the most dangerous forms of malware, known for…
Dark Adventurer Ransomware: Understanding the Threat
Ransomware is a malicious type of malware that encrypts the files on…
Property of the FBI Ransomware: A Comprehensive Guide
Ransomware is a type of malicious software that threatens to block access…
DavidHasselhoff Ransomware: Threats, Symptoms, and Removal
Ransomware is a type of malicious software (malware) that encrypts a victim's…
King Ransomware: A Comprehensive Guide
Ransomware is a form of malicious software that encrypts files on a…
Evidence of Child Pornography Ransomware: Threats and Removal Guide
Ransomware is a type of malicious software (malware) designed to deny access…
Understanding and Removing The Bully Ransomware
Ransomware is a form of malicious software (malware) designed to block access…
FoxTro Ransomware Threat: Actions, Consequences, and Removal Guide
Cyber threats are an ever-evolving challenge, and ransomware attacks remain among the…