Joker Chaos Ransomware: A Comprehensive Guide
Joker Chaos Ransomware is a menacing cyber threat designed to encrypt victims'…
AnonymousArabs Ransomware: Actions, Consequences, and Removal
AnonymousArabs Ransomware is a malicious software threat that encrypts files on the…
Gored Backdoor Malware: Removing the Trojans
Gored Backdoor is a notorious piece of malware designed to infiltrate computer…
Understanding and Removing the Trojan.Win32.Mywife Virus
The Trojan.Win32.Mywife virus stands out as a particularly insidious malware. Known for…
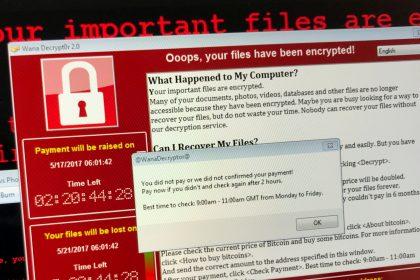
Azzasec Ransomware: Understanding the Threat and How to Protect Your Data
Ransomware remains a significant menace, continually adapting to bypass security measures and…
TL-Ver-85.2.com: A Stealthy Cyber Threat
Staying ahead of malicious actors requires constant vigilance. One such threat that…
Commercial Invoice Email Scam: A Detailed Guide
The Commercial Invoice Email Scam stands out as a particularly deceptive and…
Understanding and Mitigating the CAT DDoS Botnet Cyber Threat
The CAT DDoS Botnet represents a significant and evolving cyber threat, targeting…
SRC Ransomware: A Comprehensive Guide to Detection, Removal, and Prevention
SRC Ransomware is a pernicious cyber threat that encrypts files on an…
Oceans Ransomware: A Comprehensive Guide to Detection, Removal, and Prevention
Ransomware continues to be one of the most formidable challenges. Oceans Ransomware…