Cerker.exe Virus: A Comprehensive Guide
As technology continues to advance, so do the tactics employed by cybercriminals.…
Roundcube Unusual Login Attempt Email Scam
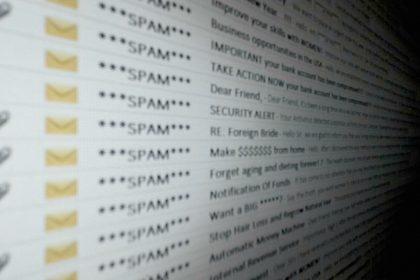
Phishing scams are deceptive attempts to acquire sensitive information, such as usernames,…
Aruba IT Email Scam: A Comprehensive Malware Removal Guide
Phishing scams are deceptive tactics used by cybercriminals to manipulate individuals into…
XIXTEXRZ Ransomware: Threats, Symptoms, and Removal Guide
Ransomware is a type of malicious software designed to deny access to…
Skotes.exe Virus: Actions, Consequences, and Removal Guide
New threats emerge daily, and one of the most concerning is the…
Behavior.Win32.AMSI.Patch: A Growing Cyber Threat
Malware like Behavior.Win32.AMSI.Patch poses significant threats to both personal and organizational systems.…
Behavior:Win32/WDBlockFirewallRule.P – A Cyber Threat to Your Security
In today’s digital landscape, the rise of cyber threats like Behavior:Win32/WDBlockFirewallRule.P poses…
ElonMuskIsGreedy Ransomware: A Malicious Threat
Ransomware is a formidable form of malware that has increasingly become a…
Spider Ransomware: A Comprehensive Threat Overview and Removal Guide
Ransomware is a particularly malicious form of malware designed to lock a…
BlackNote Stealer: A Trojan Horse Malware
Trojan horse malware, often simply referred to as "Trojans," are a form…