Clickads-hub[.]top Threat: Detection, Removal, and Prevention
In today’s digital world, online threats continue to evolve, with a variety…
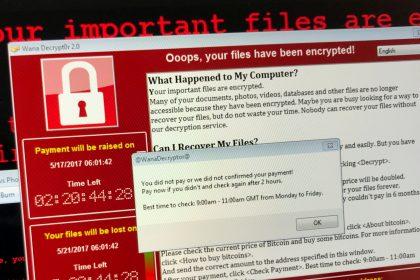
Dark Intel Ransomware: Detection, Removal, and Prevention
Introduction to Dark Intel Ransomware Dark Intel is a ransomware strain recently…
Novalock Ransomware: A Dangerous Threat to Company Networks
Novalock is a potent and malicious ransomware strain identified as part of…
JarkaStealer Trojan Malware: A Comprehensive Guide to Threat Detection and Removal
Introduction: Understanding Trojan Horse Malware Trojan horse malware, commonly referred to as…
G7 Italia Email Scam: A Comprehensive Guide to Identifying and Avoiding Phishing Threats
Phishing scams are a prevalent form of cybercrime designed to deceive individuals…
Avail AirDrop Scam: A Comprehensive Guide to Understanding and Removing This Threat
With cyber threats evolving every day, malicious actors have turned to creative…
System AV: A Deep Dive into Adware
Adware, short for advertising-supported software, is a type of malware designed to…
Kneadspro.com Adware: A Growing Digital Threat
Adware, short for advertising-supported software, is a form of malware that inundates…
MaxCat Ransomware: How to Deal With File Encryption
Ransomware is a form of malicious software designed to block access to…