PlayBoy LOCKER Ransomware: Comprehensive Removal and Prevention Guide
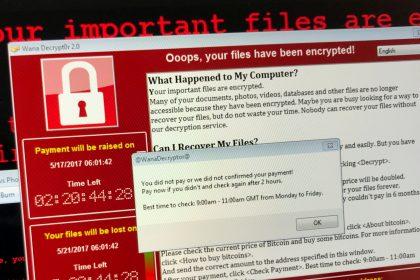
PlayBoy LOCKER is a highly dangerous ransomware that encrypts your files and…
CmbLabs Ransomware: A Sophisticated Cyber Threat That Encrypts and Extorts
Safeguarding personal and business data from cyber threats has never been more…
.V Virus File (Dharma Ransomware) Removal Guide
Dharma ransomware has long been one of the most persistent ransomware families,…
Core (Makop) Ransomware: A Guide to Removal and Prevention
Ransomware remains one of the most persistent and damaging cyber threats. One…
V (Dharma) Ransomware: Analysis and Removal Guide
Understanding V (Dharma) Ransomware V is a ransomware variant belonging to the…
LCRYPTX Ransomware: A Comprehensive Threat Analysis and Removal Guide
LCRYPTX is a ransomware-type malware that encrypts victims' files and demands a…
Revenge Of Heisenberg Ransomware
Overview of Revenge Of Heisenberg Ransomware Revenge Of Heisenberg is a ransomware…
Hitler_77777 Ransomware: Analysis and Removal Guide
The Hitler_77777 ransomware is a dangerous cryptovirus identical to TRUST FILES ransomware.…
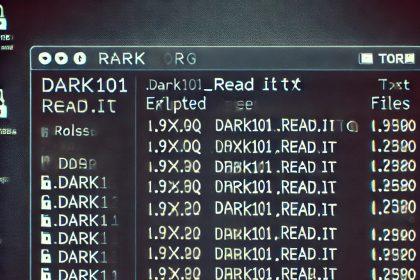
Dark 101 Ransomware: A Detailed Threat Analysis and Removal Guide
Dark 101 is a ransomware-type malware based on the Chaos framework, recently…
Bpant Ransomware: Understanding and Mitigating the Threat
If your files suddenly have the extension .Bpant and a ransom note…