Nett Ransomware: A Growing Cyber Threat
Nett ransomware is a malicious software program that encrypts files on a…
Zonix Ransomware: Understanding the Threat and How to Protect Your Systems
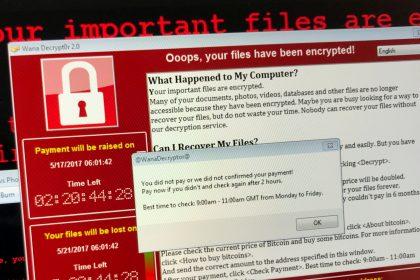
Ransomware attacks have become increasingly prevalent, posing significant threats to individuals and…
SRC Ransomware: A Comprehensive Guide to Detection, Removal, and Prevention
SRC Ransomware is a pernicious cyber threat that encrypts files on an…
Understanding the ShrinkLocker Ransomware Threat
Ransomware remains one of the most insidious and damaging forms of malware.…
Understanding and Mitigating the Edhst Ransomware Threat
Ransomware has become one of the most pervasive and damaging cyber threats…
Reload Ransomware: A Growing Cyber Threat
Reload ransomware has emerged as a formidable adversary, targeting individuals and businesses…
Scrypt Ransomware: A Comprehensive Guide
Ransomware remains one of the most pervasive and damaging cyber threats today,…
BAAA Ransomware: A Menace from the STOP/Djvu Ransomware Lineage
Amidst the expansive landscape of cyber threats, BAAA Ransomware emerges as a…
QEHU File Extension: Ransomware Strikes Again
QEHU Ransomware is yet another malware strain that is a part of…
QEPI Ransomware: A Menace from the STOP/Djvu Ransomware Lineage
QEPI Ransomware emerges as a sinister iteration within the notorious STOP/Djvu Ransomware…