Black Berserk Ransomware
The Black Berserk Virus is a dangerous ransomware infection that encrypts files…
DeathHunters Ransomware
DeathHunters is a newly discovered ransomware strain based on the Chaos ransomware…
V (Dharma) Ransomware: Analysis and Removal Guide
Understanding V (Dharma) Ransomware V is a ransomware variant belonging to the…
BlackLock Ransomware: A Analysis and Removal Guide
BlackLock is a ransomware-type virus that encrypts files and demands ransoms for…
Hunter Ransomware: A New Variant of Prince Ransomware – Removal & Prevention Guide
A new ransomware threat named Hunter has emerged, encrypting victims’ files and…
SpiderParadise Ransomware: Analysis and Removal Guide
Ransomware is one of the most dangerous types of malware, locking victims…
Mania Crypter Ransomware: Understanding and Removing the Threat
Mania Crypter is a dangerous ransomware variant based on the infamous LockBit…
EByte Locker Ransomware: A Detailed Guide to Understanding, Removing, and Preventing This Threat
What Is EByte Locker Ransomware? EByte Locker is a malicious ransomware strain…
D0glun Ransomware – Threat Analysis and Removal Guide
Ransomware continues to evolve, with new threats like D0glun targeting unsuspecting users.…
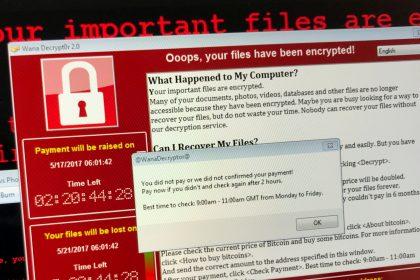
Removing WantToCry Ransomware and Preventing Future Infections
Ransomware attacks are among the most destructive cyber threats faced by individuals…