How to Adjust EDR Security Settings for Maximum Threat Defense
You’ve got EDR (Endpoint Detection and Response) software. Great. But here’s the…
“Purchase Order And Quotation Of Best Price” Scam: A Phishing Attempt Disguised as a Business Inquiry
The "Purchase Order And Quotation Of Best Price" scam email is a…
AllCiphered Ransomware: Understanding the Threat and How to Protect Yourself
The AllCiphered ransomware is a dangerous cyber threat that belongs to the…
“Email Address Included In The Blacklist” Phishing Scam: How to Recognize, Avoid, and Remove It
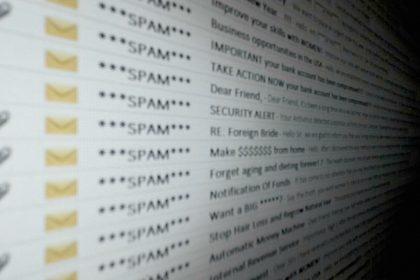
Online scams have become more sophisticated, often targeting unsuspecting users through phishing…
Debt Recovery and Delivery Team Donald Trump: A Phishing Scam You Should Know About
Phishing scams are fraudulent activities designed to deceive individuals into revealing personal…
Muck Stealer Trojan Horse Malware and Protecting Your System
Trojan horse malware, or simply "Trojans," is a deceptive type of cyber…
Trojan:Win32/Stealcmtb Malware Threat: What You Need to Know & How to Remove It Effectively
Trojan horse malware, commonly referred to as "Trojans," represents a significant cybersecurity…
Allarich Ransomware: Understanding the Threat
Ransomware is a form of malicious software (malware) that cybercriminals use to…
“Verify Delivery Error” Email Scam: Defending Agains Malicious Emails
Phishing scams have become increasingly sophisticated, preying on unsuspecting users through deceptive…
WorldTracker Info-Stealer: A Trojan Horse Malware
Trojan horse malware, commonly referred to simply as "Trojans," represents one of…