Automated Remediation Tools: Streamlining Cybersecurity for Businesses
Meta Description: Automate threat response with automated remediation tools to protect your business, reduce downtime, and enhance cybersecurity efficiency. In today’s…
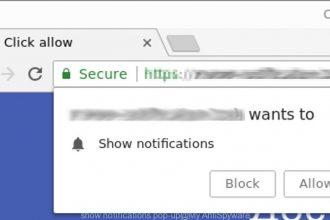
Cynovira.com Ads
Cynovira.com ads are intrusive browser notifications and redirects generated by a deceptive website that tricks users into allowing push notifications. Once…
PromptSpy
PromptSpy is an advanced Android spyware that uses generative AI to help it stay active on infected devices. Once installed, it…
BoryptGrab Stealer
BoryptGrab Stealer is a dangerous data‑stealing malware targeting Windows systems. It spreads through fake software downloads and is designed to harvest…
Pornhits.com
Pornhits.com redirects can expose your browser to intrusive ads, tracking scripts, and potentially unwanted programs (PUPs). If your browser suddenly opens…
Valrelio.co.in Scam
Valrelio.co.in is a deceptive website designed to trick users into enabling malicious browser notifications that can lead to scams, malware,…
Massiv Trojan
Massiv is a dangerous Android banking trojan that disguises itself as a legitimate IPTV streaming application.Once installed, it quietly gains…
Cybersecurity Posture Management: Strengthening Your Business Defenses
Strengthen your business cybersecurity posture with proactive management strategies, advanced threat prevention, and multi-device protection.
iScans Fake Crypto Tracker
The iScans Fake Crypto Tracker virus is a malicious crypto-themed scam platform designed to trick users into believing they have cryptocurrency…
QuickLens – Search Screen with Google Lens Virus
QuickLens – Search Screen with Google Lens is a malicious browser extension that disguises itself as a helpful tool for searching…