Ransomware is a form of malicious software (malware) that encrypts a victim’s files or locks them out of their system, demanding a ransom payment to restore access. It is one of the most disruptive types of cyber threats due to its capacity to cripple both individual and organizational operations. Ransomware typically spreads through phishing emails, malicious downloads, or vulnerabilities in outdated software, and its primary objective is financial gain from its victims.
Griffin Ransomware: A Detailed Threat Overview
Griffin Ransomware is a particularly insidious variant of ransomware designed to lock files on infected systems, rendering them inaccessible until a ransom is paid. Once Griffin Ransomware infects a system, it executes several steps to ensure its malicious activities are carried out effectively.
The malware usually infiltrates a system via phishing emails that contain malicious attachments or links. It can also exploit vulnerabilities in software to gain access. After installation, Griffin Ransomware encrypts the victim’s files using advanced encryption algorithms, making them unreadable. It appends a specific file extension to the encrypted files, such as .griffin, signaling their compromised state.
Consequences and Ransom Note
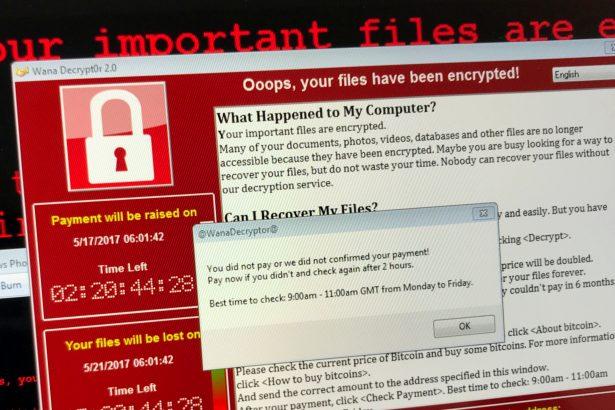
The primary consequence of Griffin Ransomware is the encryption of critical files, which disrupts access to important documents, photos, and other data. The ransomware typically leaves a ransom note on the infected system, which can be found in a text file or an image placed in prominent locations on the desktop or within folders. The ransom note provides instructions on how to contact the attackers and details the amount of ransom demanded, often in cryptocurrency like Bitcoin. It may also threaten to delete the encrypted files if the ransom is not paid within a specified timeframe.
Purpose and Impact
The general purpose of Griffin Ransomware, like other ransomware variants, is to extort money from victims by leveraging their need for the locked files. It poses a significant threat to both individuals and organizations by causing data loss and disrupting normal operations. The attackers’ goal is to maximize their financial gain by creating a sense of urgency and fear in the victims.
Symptoms of Griffin Ransomware Infection
- File Inaccessibility: Files become unreadable and display an unfamiliar file extension.
- Ransom Note: Presence of a ransom note on the desktop or in various folders.
- Unusual System Behavior: Sluggish performance or sudden system crashes.
- Encryption Alerts: Notifications about encrypted files or inability to open important documents.
Detection Names
If you suspect Griffin Ransomware might be on your system, you can look for detection names such as:
- Griffin ransomware
- .griffin file extension
- Ransom:Win32/Griffin
Similar Threats
Other ransomware variants similar to Griffin include:
- WannaCry: Notorious for its global ransomware attack exploiting a Windows vulnerability.
- Ryuk: Known for targeting high-profile organizations and demanding large ransoms.
- Sodinokibi (REvil): Another aggressive ransomware known for its extortion tactics and data leaks.
Comprehensive Removal Guide
- Boot into Safe Mode: Restart your computer and press F8 (or Shift + F8) before Windows loads to enter Safe Mode. This limits the ransomware’s ability to interfere.
- Disconnect from the Internet: Unplug your internet connection to prevent further communication with the ransomware servers.
- Use Anti-Malware Software:
- Download and install SpyHunter.
- Update the software to ensure it has the latest virus definitions.
- Perform a full system scan to detect and remove Griffin Ransomware.
- Manually Remove Residual Files:
- Open Task Manager (Ctrl + Shift + Esc) and end any processes related to Griffin Ransomware.
- Delete any suspicious files or folders related to the ransomware from your system.
- Restore Your Files:
- Use backups if available to restore encrypted files. Ensure these backups are free from ransomware.
- Consider using file recovery tools or decryptors provided by security researchers, if available.
- Change Passwords: Update passwords for accounts that may have been compromised.
Prevention Tips
To prevent ransomware infections like Griffin, consider these actions:
- Regular Backups: Maintain up-to-date backups of critical files on an external drive or cloud service.
- Security Updates: Regularly update your operating system and software to patch vulnerabilities.
- Email Caution: Be wary of email attachments and links from unknown or untrusted sources.
- Use Security Software: Install and maintain reliable anti-malware software, such as SpyHunter, which offers real-time protection.
For comprehensive protection and removal of malware like Griffin Ransomware, download SpyHunter. SpyHunter offers a free scan to detect threats and provide effective removal solutions.
If you are still having trouble, consider contacting remote technical support options.