KRUU Ransomware Joins the STOP/Djvu Ransomware Family
Like its variant siblings from the STOP/Djvu Ransomware family, KRUU Ransomware has been discovered encrypting files and then demanding a ransom in order to restore file access. If you tend to install applications from misleading or potentially unreliable third-party sites, you may end up exposing yourself to threats like KRUU Ransomware.
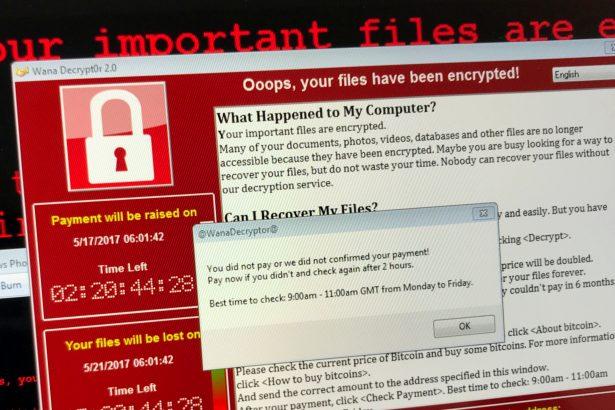
KRUU Ransomware corrupts and encrypts multiple file types, including photos, music, documents, and videos. During the encryption, KRUU Ransomware will append the .KRUU file extension to affected files and will then leave a ransom note named README.txt on the user’s desktop and in every folder containing encrypted files.
Unfortunately, a decryption tool that would unlock files encrypted by KRUU Ransomware is not available at the moment, and the only reliable way to recover infected files is to restore them from a backup or possibly use alternative data recovery options. However, there’s also no guarantee that alternative data recovery tools will unlock all the encrypted files.
Although the cybercriminals behind KRUU Ransomware promise to provide a decryptor for a ransom payment, you may never receive any decryption tools even if you pay.
KRUU Ransomware spreads similarly to the other STOP/Djvu family variants. It generally happens via malicious spam emails or when users download pirated software from peer-to-peer and other unreliable file-sharing sites that could be laced with malware. All programs from this group follow the same behavioral pattern: the moment target files are encrypted, they demand a ransom in exchange for the decryption key. KRUU Ransomware asks for $980 for decryption, but the hackers will offer a 50% discount if contact is established within the first 72 hours after infection at either manager@time2mail.ch or supportsys@airmail.cc.
How Do I Deal with a KRUU Ransomware Attack?
To protect yourself from a KRUU Ransomware attack, you should have a reputable malware remediation tool installed on your computer. That way, you can constantly scan for elements associated with this troublesome ransomware infection and other malware threats.