A new ransomware threat named Hunter has emerged, encrypting victims’ files and demanding payment in cryptocurrency for decryption. Hunter ransomware is based on Prince ransomware, a previously known malware family. This ransomware appends the .Hunter extension to encrypted files and drops a ransom note titled “Decryption Instructions.txt.” Additionally, it modifies the victim’s desktop wallpaper to reinforce its ransom demand.
- Hunter Ransomware Overview
- How Hunter Ransomware Works
- Hunter Ransomware Ransom Note
- How Did Hunter Ransomware Infect My Computer?
- How to Remove Hunter Ransomware
- Scan Your Computer for Free with SpyHunter
- Step 1: Scan and Remove Hunter Ransomware Using SpyHunter
- Step 2: Restore Encrypted Files
- How to Protect Your System from Ransomware
- Conclusion
Victims are instructed to contact attack-tw1337@proton.me for further instructions. However, paying the ransom is not recommended, as there is no guarantee that cybercriminals will provide the decryption key.
Hunter Ransomware Overview
Threat Summary
| Attribute | Details |
|---|---|
| Name | Hunter Ransomware |
| Threat Type | Ransomware, File Locker |
| Encrypted File Extension | .Hunter |
| Ransom Note File Name | Decryption Instructions.txt |
| Contact Email | attack-tw1337@proton.me |
| Detection Names | Avast (Win32:Dh-A [Heur]), Combo Cleaner (Generic.Ransom.Prince.A.2D1448B6), ESET-NOD32 (A Variant Of WinGo/Filecoder.HG), Kaspersky (HEUR:Trojan-Ransom.Win64.Generic), Microsoft (Ransom:Win64/PrinceRansom.YAA!MTB) |
| Symptoms of Infection | Files encrypted with .Hunter extension, ransom note appears, wallpaper changed, files become inaccessible |
| Damage | Data encryption, financial loss, potential for additional malware infections |
| Distribution Methods | Malicious email attachments, infected software downloads, phishing websites, torrent sites |
| Danger Level | High |
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!
How Hunter Ransomware Works
Hunter ransomware follows a five-step attack sequence, similar to other ransomware variants:
Initial Infection
Hunter infiltrates systems via:
- Malicious email attachments (often disguised as invoices, job applications, or other legitimate files).
- Infected downloads (pirated software, fake updates, or cracked applications).
- Compromised websites and ads (drive-by downloads triggered by visiting an infected page).
- Exploited software vulnerabilities (outdated software with security gaps).
File Encryption
Once executed, Hunter scans the system for targeted file types, including:
- Documents (
.docx,.xlsx,.pdf) - Images (
.jpg,.png,.gif) - Videos (
.mp4,.mov) - Databases (
.sql,.mdb) - Executable files (
.exe)
Each file is encrypted with a strong cryptographic algorithm, and the .Hunter extension is appended.
Example:
photo.jpg→photo.jpg.Hunterdocument.pdf→document.pdf.Hunter
Ransom Note Drop
After encryption, Hunter places "Decryption Instructions.txt" on the desktop and inside affected folders.
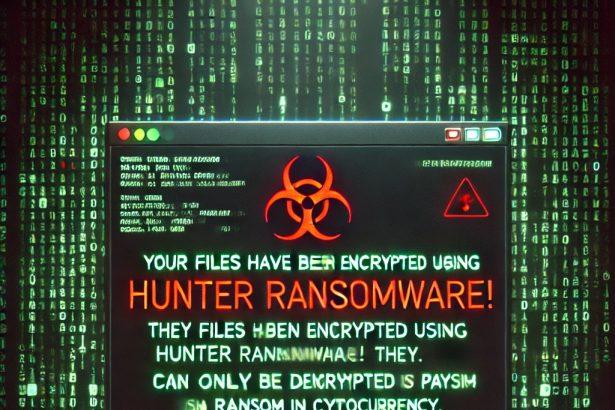
Desktop Wallpaper Change
The ransomware modifies the victim’s wallpaper to further intimidate them.
Ransom Demand
The ransom note provides instructions to email attack-tw1337@proton.me for payment instructions.
Hunter Ransomware Ransom Note
Below is the text displayed in the Hunter ransomware ransom note:
---------- Hunter Ransomware ----------
Your files have been encrypted using Hunter Ransomware!
They can only be decrypted by paying us a ransom in cryptocurrency.
Encrypted files have the .hunter extension.
IMPORTANT: Do not modify or rename encrypted files, as they may become unrecoverable.
Contact us at the following email address to discuss payment.
attack-tw1337@proton.me
---------- Hunter Ransomware ----------How Did Hunter Ransomware Infect My Computer?
Hunter ransomware spreads through multiple attack vectors:
- Email Attachments (Phishing Campaigns)
- Hackers send fraudulent emails with infected attachments disguised as:
- Invoices
- Shipping updates
- Bank statements
- Job offers
- These attachments contain macro-enabled documents, ZIP files, or JavaScript files that execute malware.
- Hackers send fraudulent emails with infected attachments disguised as:
- Fake Software Downloads
- Cybercriminals often bundle ransomware with pirated software, cracks, or key generators.
- Downloading from torrent sites, free file-sharing platforms, or unverified sources increases risk.
- Compromised Websites & Drive-By Downloads: Visiting infected websites or clicking on malicious ads can trigger automatic downloads.
- Exploiting Software Vulnerabilities: Outdated applications and unpatched Windows OS are prime targets for ransomware exploits.
How to Remove Hunter Ransomware
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!
Step 1: Scan and Remove Hunter Ransomware Using SpyHunter
SpyHunter is a powerful anti-malware tool capable of detecting and removing Hunter ransomware and related threats.
Download and Install SpyHunter
- Run the installer and follow the on-screen instructions.
- Launch SpyHunter after installation.
Perform a Full System Scan
- Click "Start Scan" to check for Hunter ransomware infections.
- Wait for SpyHunter to detect all threats.
Remove Hunter Ransomware
- Select Hunter ransomware and related malware from the scan results.
- Click "Fix Threats" to eliminate them.
Step 2: Restore Encrypted Files
Since no free decryptor exists, victims have limited options for recovering encrypted files:
Restore from Backup
- If you have external backups or cloud storage, restore files from there.
Use Windows Previous Versions
- Right-click the encrypted file > Properties > Previous Versions tab.
- Restore an earlier version if available.
Try Data Recovery Software
- Tools like EaseUS Data Recovery Wizard or Recuva may recover deleted copies of files.
How to Protect Your System from Ransomware
Preventing ransomware requires strong cybersecurity practices:
- Use a Reliable Anti-Malware Solution: Install SpyHunter to detect and prevent ransomware attacks.
- Regularly Update Software & OS: Keep Windows, antivirus, and third-party applications up to date.
- Avoid Suspicious Emails & Links: Do not open attachments from unknown senders. Hover over links before clicking to verify legitimacy.
- Disable Macros in Microsoft Office: Cybercriminals often use macro-enabled documents to execute ransomware.
- Use a Firewall & Network Security Tools: Block unauthorized network access.
- Backup Your Data: Store backups on external drives or secure cloud storage.
- Avoid Untrusted Websites & Software: Download applications only from official sources.
Conclusion
Hunter ransomware, derived from Prince ransomware, is a dangerous threat that encrypts user files and demands payment. Victims are advised not to pay the ransom, as there is no guarantee of file recovery. Instead, SpyHunter can remove the infection, while backup strategies and security best practices can prevent future attacks.
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!